1
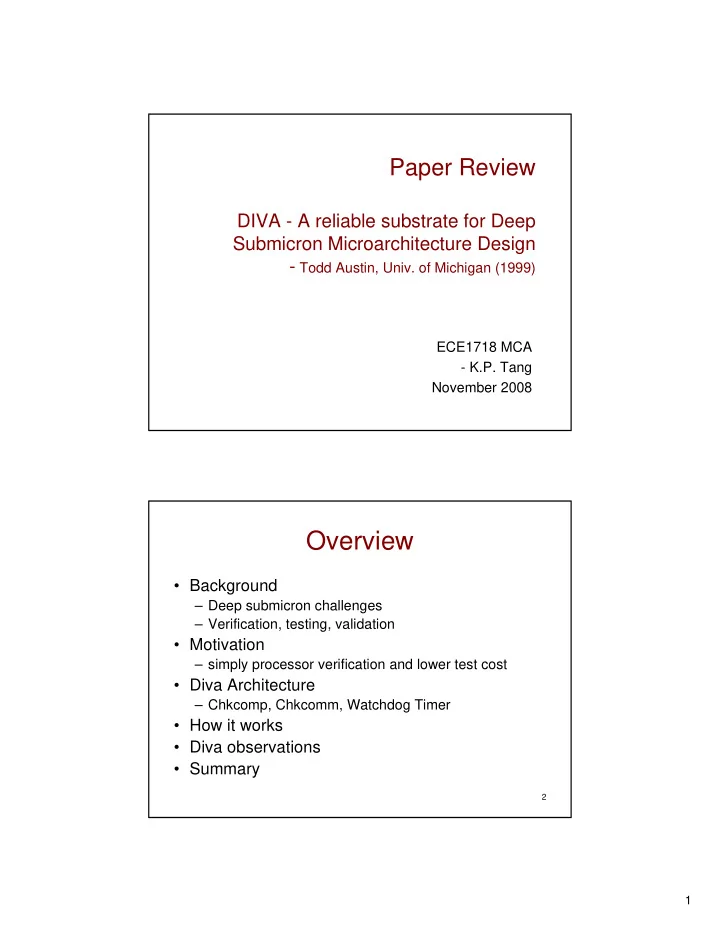
Paper Review
DIVA - A reliable substrate for Deep Submicron Microarchitecture Design
- Todd Austin, Univ. of Michigan (1999)
ECE1718 MCA
- K.P. Tang
November 2008
2
Overview
- Background
– Deep submicron challenges – Verification, testing, validation
- Motivation
– simply processor verification and lower test cost
- Diva Architecture
– Chkcomp, Chkcomm, Watchdog Timer
- How it works
- Diva observations
- Summary