Uni Innsbruck Uni Innsbruck Informatik Informatik -
- 1
1
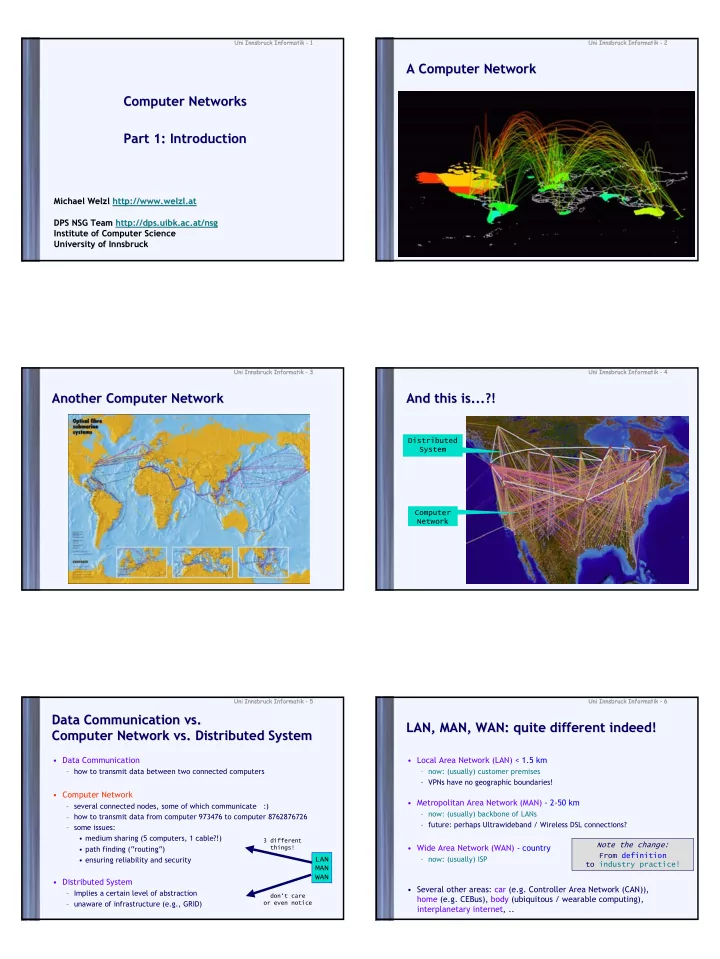
Computer Networks Computer Networks Part 1: Introduction Part 1: Introduction
Michael Welzl Michael Welzl http://www.welzl.at http://www.welzl.at DPS NSG Team DPS NSG Team http://dps.uibk.ac.at/nsg http://dps.uibk.ac.at/nsg Institute of Computer Science Institute of Computer Science University of Innsbruck University of Innsbruck
Uni Innsbruck Uni Innsbruck Informatik Informatik -
- 2
2
A Computer Network A Computer Network
Uni Innsbruck Uni Innsbruck Informatik Informatik -
- 3
3
Another Computer Network Another Computer Network
Uni Innsbruck Uni Innsbruck Informatik Informatik -
- 4
4
And this is...?! And this is...?!
Computer Network Distributed System
Uni Innsbruck Uni Innsbruck Informatik Informatik -
- 5
5
Data Communication vs. Data Communication vs. Computer Network vs. Distributed System Computer Network vs. Distributed System
- Data Communication
– how to transmit data between two connected computers
- Computer Network
– several connected nodes, some of which communicate :) – how to transmit data from computer 973476 to computer 8762876726 – some issues:
- medium sharing (5 computers, 1 cable?!)
- path finding (“routing“)
- ensuring reliability and security
- Distributed System
– Implies a certain level of abstraction – unaware of infrastructure (e.g., GRID) LAN MAN WAN
3 different things! don‘t care
- r even notice
Uni Innsbruck Uni Innsbruck Informatik Informatik -
- 6
6
LAN, MAN, WAN: quite different indeed! LAN, MAN, WAN: quite different indeed!
- Local Area Network (LAN) < 1.5 km
– now: (usually) customer premises – VPNs have no geographic boundaries!
- Metropolitan Area Network (MAN) - 2-50 km
– now: (usually) backbone of LANs – future: perhaps Ultrawideband / Wireless DSL connections?
- Wide Area Network (WAN) - country
– now: (usually) ISP Note the change: From definition to industry practice!
- Several other areas: car (e.g. Controller Area Network (CAN)),
home (e.g. CEBus), body (ubiquitous / wearable computing), interplanetary internet, ..