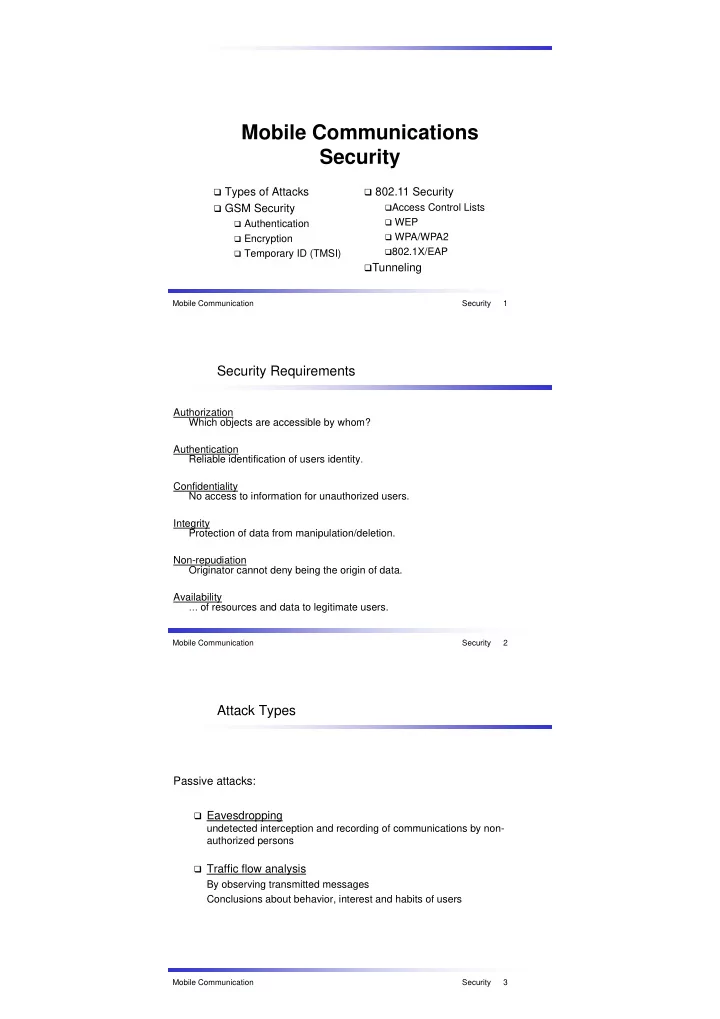
SLIDE 3 GSM / UMTS security mechanisms
User Authentication (cont.)
Suppose a mobile station i enters a new cell (eg in a foreign network).
Th A th i ti C t (AC) t th HLR i th t t d b th
The Authorization Center (AC) at the users HLR is then contacted by the
foreign network.
The AC generates a random number RAND (128 bit) and a value SRES
g ( ) (32 bit) by employing A3 with Ki to RAND.
HLR sends (RAND, SRES) encrypted and signed to the foreign network. The foreign network sends RAND (challenge) to the mobile station i and
„asks“ it to calculate SRES‘ by executing A3 with Ki on RAND.
Then the mobile station sends calculated SRES‘ back to foreign network Then the mobile station sends calculated SRES back to foreign network
(response).
If SRES = SRES‘ the mobile station is authenticated successfully. Security Mobile Communication Security 7
GSM / UMTS security mechanisms
Encryption of the air interface (optional)
The challenge response method cannot prevent „Man in the Middle“ attacks
E d i d th i d h ll th f th
Eavesdropping and unauthorized phone calls on the expense of others
Therefore, there is another one way function in GSM called "A8 algorithm" A8 is also determined by the network operator, e.g. also COMP128-3
y p , g
HLR generates a symmetric key Kc from RAND and Ki by A8 HLR sends (RAND, SRES, Kc) encrypted and signed to the foreign network. The foreign network sends RAND to mobile station as before. The mobile station computes Kc using RAND and Ki employing A8 K i th
d th i i t f ti k
Kc is then used on the air interface as an encryption key. Security Mobile Communication Security 8
GSM / UMTS security mechanisms
Encryption of the Air interface (optional, cont.)
With Kc all calls between mobile and base station are encrypted.
Th ti l ith it lf i ll d A5 l ith “ i GSM
The encryption algorithm itself is called „A5-algorithm“ in GSM There are 3 different standardizedA5:
A5/1 stream cipher algorithm, weak
p g ,
A5/2 stream cipher algorithm, even weaker A5/3 block cipher algorithm, strong
http://www.gsmworld.com/using/algorithms/index.shtml
Security Mobile Communication Security 9