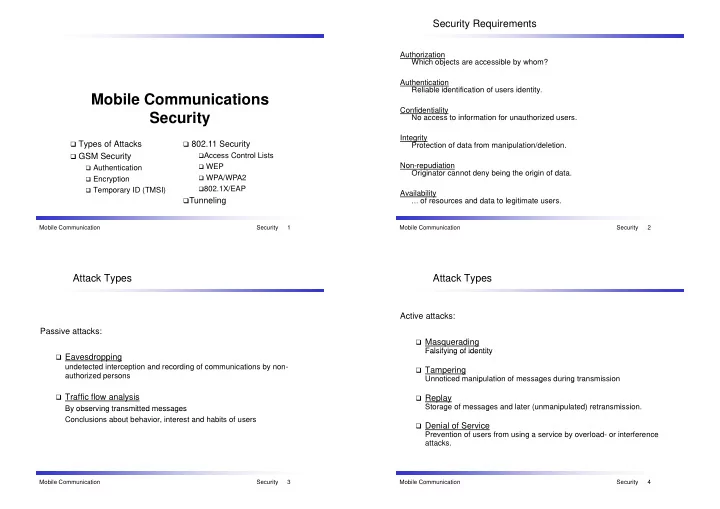
Mobile Communications Mobile Communications Security
Types of Attacks GSM Security 802.11 Security
Access Control Lists
GSM Security
Authentication Encryption Access Control Lists WEP WPA/WPA2 Temporary ID (TMSI) 802.1X/EAP
Tunneling
Mobile Communication Security 1
Security Requirements
Authorization Which objects are accessible by whom? Authentication Reliable identification of users identity. Confidentiality No access to information for unauthorized users. Integrity Protection of data from manipulation/deletion. Non-repudiation Originator cannot deny being the origin of data. Availability
… of resources and data to legitimate users.
Sicherheit Mobile Communication Security 2
Attack Types
Passive attacks:
Eavesdropping
undetected interception and recording of communications by non- authorized persons
Traffic flow analysis
By observing transmitted messages By observing transmitted messages Conclusions about behavior, interest and habits of users
Security Mobile Communication Security 3
Attack Types
Active attacks:
Masquerading
Falsifying of identity Falsifying of identity
Tampering
Unnoticed manipulation of messages during transmission p g g
Replay
Storage of messages and later (unmanipulated) retransmission. g g ( p )
Denial of Service
Prevention of users from using a service by overload- or interference attacks.
Security Mobile Communication Security 4