Security II: Web authentication
Markus Kuhn
Computer Laboratory, University of Cambridge https://www.cl.cam.ac.uk/teaching/1718/SecurityII/
These notes are provided as an aid for following the lectures, and are not a substitute for attending
Lent 2018 – Part II
websecurity-slides-4up.pdf 2018-02-23 11:38 fca1bee 1
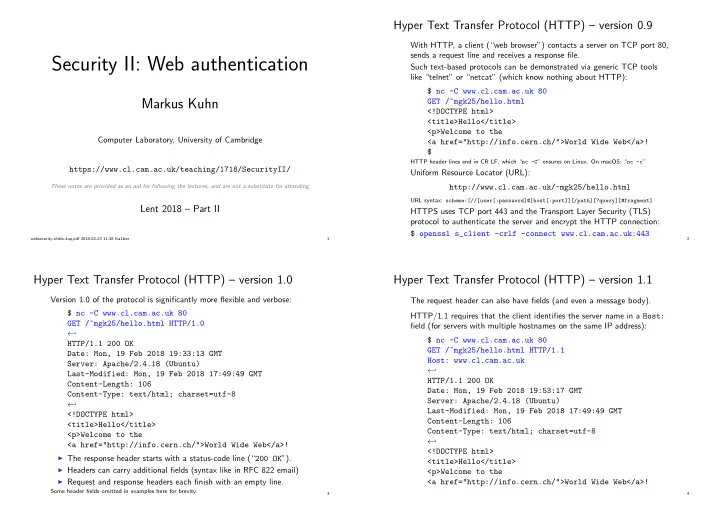
Hyper Text Transfer Protocol (HTTP) – version 0.9
With HTTP, a client (“web browser”) contacts a server on TCP port 80, sends a request line and receives a response file. Such text-based protocols can be demonstrated via generic TCP tools like “telnet” or “netcat” (which know nothing about HTTP): $ nc -C www.cl.cam.ac.uk 80 GET /~mgk25/hello.html <!DOCTYPE html> <title>Hello</title> <p>Welcome to the <a href="http://info.cern.ch/">World Wide Web</a>! $
HTTP header lines end in CR LF, which “nc -C” ensures on Linux. On macOS: “nc -c”
Uniform Resource Locator (URL): http://www.cl.cam.ac.uk/~mgk25/hello.html
URL syntax: scheme:[//[user[:password]@]host[:port]][/path][?query][#fragment]
HTTPS uses TCP port 443 and the Transport Layer Security (TLS) protocol to authenticate the server and encrypt the HTTP connection: $ openssl s_client -crlf -connect www.cl.cam.ac.uk:443
2
Hyper Text Transfer Protocol (HTTP) – version 1.0
Version 1.0 of the protocol is significantly more flexible and verbose: $ nc -C www.cl.cam.ac.uk 80 GET /~mgk25/hello.html HTTP/1.0 ← ֓ HTTP/1.1 200 OK Date: Mon, 19 Feb 2018 19:33:13 GMT Server: Apache/2.4.18 (Ubuntu) Last-Modified: Mon, 19 Feb 2018 17:49:49 GMT Content-Length: 106 Content-Type: text/html; charset=utf-8 ← ֓ <!DOCTYPE html> <title>Hello</title> <p>Welcome to the <a href="http://info.cern.ch/">World Wide Web</a>!
◮ The response header starts with a status-code line (“200 OK”). ◮ Headers can carry additional fields (syntax like in RFC 822 email) ◮ Request and response headers each finish with an empty line. Some header fields omitted in examples here for brevity.
3
Hyper Text Transfer Protocol (HTTP) – version 1.1
The request header can also have fields (and even a message body). HTTP/1.1 requires that the client identifies the server name in a Host: field (for servers with multiple hostnames on the same IP address): $ nc -C www.cl.cam.ac.uk 80 GET /~mgk25/hello.html HTTP/1.1 Host: www.cl.cam.ac.uk ← ֓ HTTP/1.1 200 OK Date: Mon, 19 Feb 2018 19:53:17 GMT Server: Apache/2.4.18 (Ubuntu) Last-Modified: Mon, 19 Feb 2018 17:49:49 GMT Content-Length: 106 Content-Type: text/html; charset=utf-8 ← ֓ <!DOCTYPE html> <title>Hello</title> <p>Welcome to the <a href="http://info.cern.ch/">World Wide Web</a>!
4