Message Authentication Codes (MACs)
Message Authentication Codes (MACs)
Jim Royer
Introduction to Cryptography
October 4, 2018
Crypto | Introduction to Cryptography | October 4, 2018 1 / 9 Message Authentication Codes (MACs)
References
”Message Authentication Codes (MACs),” Chapter 12 of Understanding Cryptography by Paar & Pelzl Message Authentication Code from Wikipedia https: //en.wikipedia.org/wiki/Message_authentication_code
Crypto | Introduction to Cryptography | October 4, 2018 2 / 9 Message Authentication Codes (MACs)
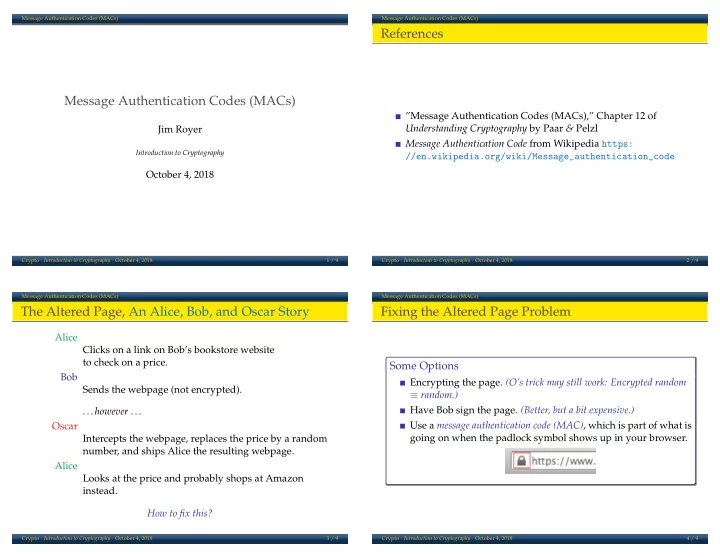
The Altered Page, An Alice, Bob, and Oscar Story
Alice Clicks on a link on Bob’s bookstore website to check on a price. Bob Sends the webpage (not encrypted). ... however ... Oscar Intercepts the webpage, replaces the price by a random number, and ships Alice the resulting webpage. Alice Looks at the price and probably shops at Amazon instead. How to fix this?
Crypto | Introduction to Cryptography | October 4, 2018 3 / 9 Message Authentication Codes (MACs)
Fixing the Altered Page Problem
Some Options
Encrypting the page. (O’s trick may still work: Encrypted random ≡ random.) Have Bob sign the page. (Better, but a bit expensive.) Use a message authentication code (MAC), which is part of what is going on when the padlock symbol shows up in your browser.
Crypto | Introduction to Cryptography | October 4, 2018 4 / 9