1
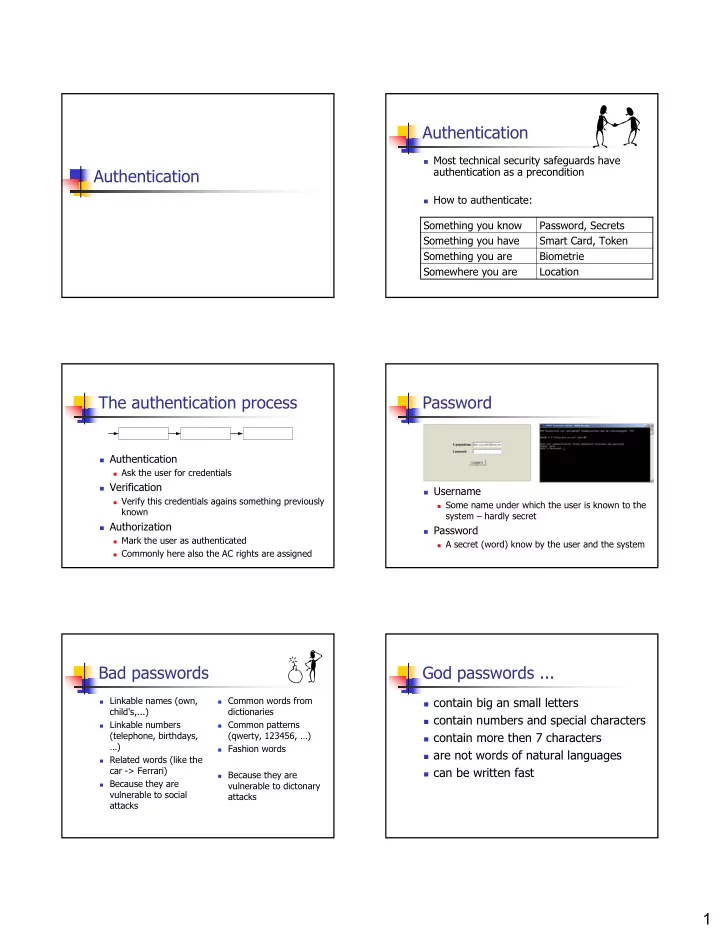
Authentication Authentication
Most technical security safeguards have
authentication as a precondition
How to authenticate:
Location Somewhere you are Biometrie Something you are Smart Card, Token Something you have Password, Secrets Something you know
The authentication process
Authentication
Ask the user for credentials
Verification
Verify this credentials agains something previously
known
Authorization
Mark the user as authenticated Commonly here also the AC rights are assigned
Password
Username
Some name under which the user is known to the
system – hardly secret
Password
A secret (word) know by the user and the system
Bad passwords
Linkable names (own,
child's,...)
Linkable numbers
(telephone, birthdays, …)
Related words (like the
car -> Ferrari)
Because they are
vulnerable to social attacks
Common words from
dictionaries
Common patterns
(qwerty, 123456, …)
Fashion words Because they are
vulnerable to dictonary attacks
God passwords ...
contain big an small letters contain numbers and special characters contain more then 7 characters are not words of natural languages can be written fast