Security 1 - Passwords
Computer security is a big and kind of dramatic area which lends itself to movie plots and fear. There are real threats our there, but staying safe is not that hard.
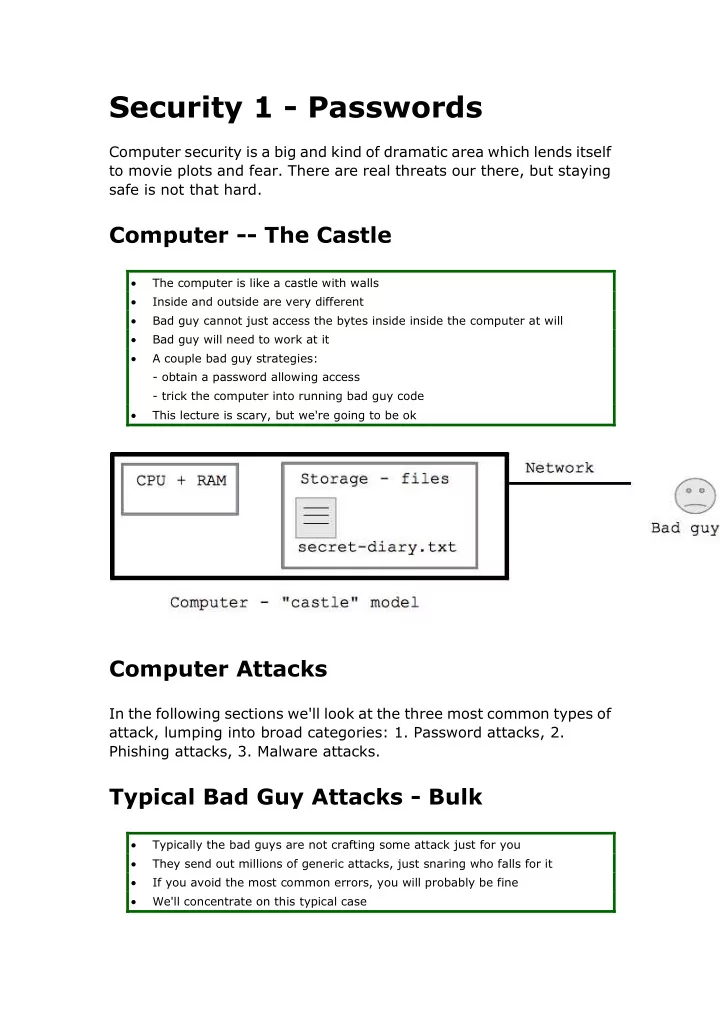
Computer -- The Castle
The computer is like a castle with walls Inside and outside are very different Bad guy cannot just access the bytes inside inside the computer at will Bad guy will need to work at it A couple bad guy strategies:
- obtain a password allowing access
- trick the computer into running bad guy code
This lecture is scary, but we're going to be ok
Computer Attacks
In the following sections we'll look at the three most common types of attack, lumping into broad categories: 1. Password attacks, 2. Phishing attacks, 3. Malware attacks.
Typical Bad Guy Attacks - Bulk
Typically the bad guys are not crafting some attack just for you They send out millions of generic attacks, just snaring who falls for it If you avoid the most common errors, you will probably be fine We'll concentrate on this typical case