1
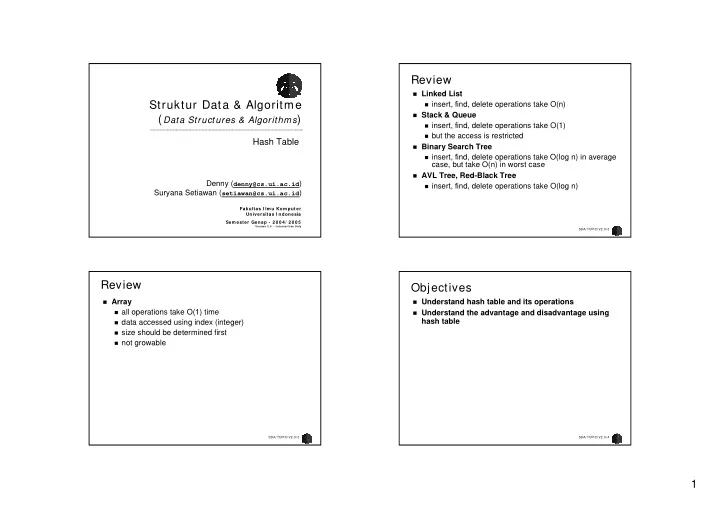
Struktur Data & Algoritme ( Data Structures & Algorithms)
Denny (denny@cs.ui.ac.id) Suryana Setiawan (setiawan@cs.ui.ac.id)
Fakultas I lm u Kom puter Universitas I ndonesia Sem ester Genap - 2 0 0 4 / 2 0 0 5
Version 2 .0 - I nternal Use Only
Hash Table
SDA/ TOPIC/ V2.0/ 2
Review
Linked List insert, find, delete operations take O(n) Stack & Queue insert, find, delete operations take O(1) but the access is restricted Binary Search Tree insert, find, delete operations take O(log n) in average
case, but take O(n) in worst case
AVL Tree, Red-Black Tree insert, find, delete operations take O(log n)
SDA/ TOPIC/ V2.0/ 3
Review
Array all operations take O(1) time data accessed using index (integer) size should be determined first not growable
SDA/ TOPIC/ V2.0/ 4
Objectives
Understand hash table and its operations Understand the advantage and disadvantage using