EDA222/DIT160 – Real-Time Systems, Chalmers/GU, 2008/2009 Lecture #10
Updated 2009-02-15
1
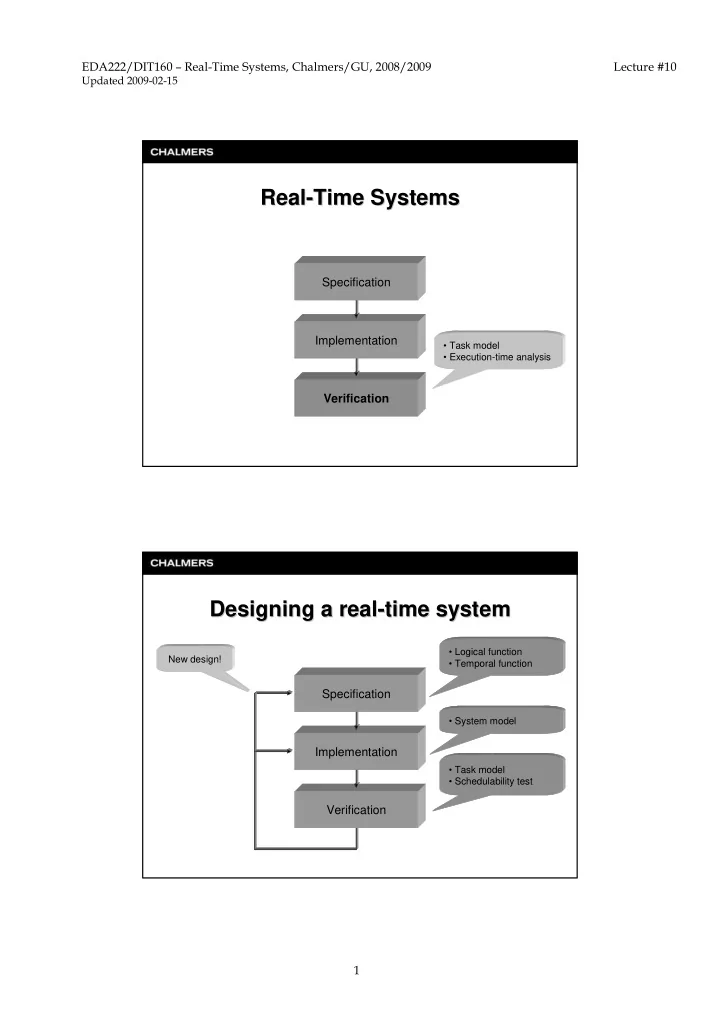
Real Real-
- Time Systems
Time Systems
Verification Implementation Specification
- Task model
- Execution-time analysis
Designing a real Designing a real-
- time system
time system
Verification Implementation Specification
How should it be done? What should be done & When should it be done? Can it be done with the given implementation? New design!
- Task model
- Schedulability test
- Logical function
- Temporal function
- System model