Randomized Computation
Nabil Mustafa Computability and Complexity
Nabil Mustafa Randomized ComputationPolynomial Identity Testing
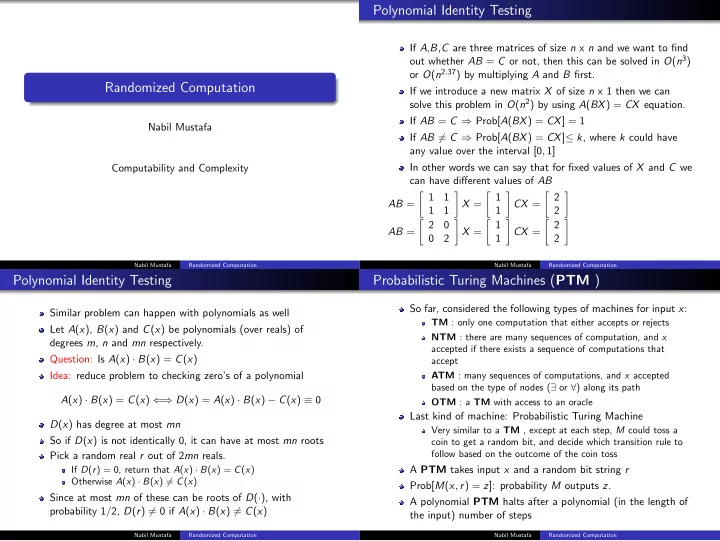
If A,B,C are three matrices of size n x n and we want to find
- ut whether AB = C or not, then this can be solved in O(n3)
- r O(n2.37) by multiplying A and B first.
If we introduce a new matrix X of size n x 1 then we can solve this problem in O(n2) by using A(BX) = CX equation. If AB = C ⇒ Prob[A(BX) = CX] = 1 If AB = C ⇒ Prob[A(BX) = CX]≤ k, where k could have any value over the interval [0, 1] In other words we can say that for fixed values of X and C we can have different values of AB AB = 1 1 1 1
- X =
1 1
- CX =
2 2
- AB =
2 2
- X =
1 1
- CX =
2 2
- Nabil Mustafa
Polynomial Identity Testing
Similar problem can happen with polynomials as well Let A(x), B(x) and C(x) be polynomials (over reals) of degrees m, n and mn respectively. Question: Is A(x) · B(x) = C(x) Idea: reduce problem to checking zero’s of a polynomial A(x) · B(x) = C(x) ⇐ ⇒ D(x) = A(x) · B(x) − C(x) ≡ 0 D(x) has degree at most mn So if D(x) is not identically 0, it can have at most mn roots Pick a random real r out of 2mn reals. If D(r) = 0, return that A(x) · B(x) = C(x) Otherwise A(x) · B(x) = C(x) Since at most mn of these can be roots of D(·), with probability 1/2, D(r) = 0 if A(x) · B(x) = C(x)
Nabil Mustafa Randomized ComputationProbabilistic Turing Machines (PTM )
So far, considered the following types of machines for input x: TM : only one computation that either accepts or rejects NTM : there are many sequences of computation, and x accepted if there exists a sequence of computations that accept ATM : many sequences of computations, and x accepted based on the type of nodes (∃ or ∀) along its path OTM : a TM with access to an oracle Last kind of machine: Probabilistic Turing Machine Very similar to a TM , except at each step, M could toss a coin to get a random bit, and decide which transition rule to follow based on the outcome of the coin toss A PTM takes input x and a random bit string r Prob[M(x, r) = z]: probability M outputs z. A polynomial PTM halts after a polynomial (in the length of the input) number of steps
Nabil Mustafa Randomized Computation