1
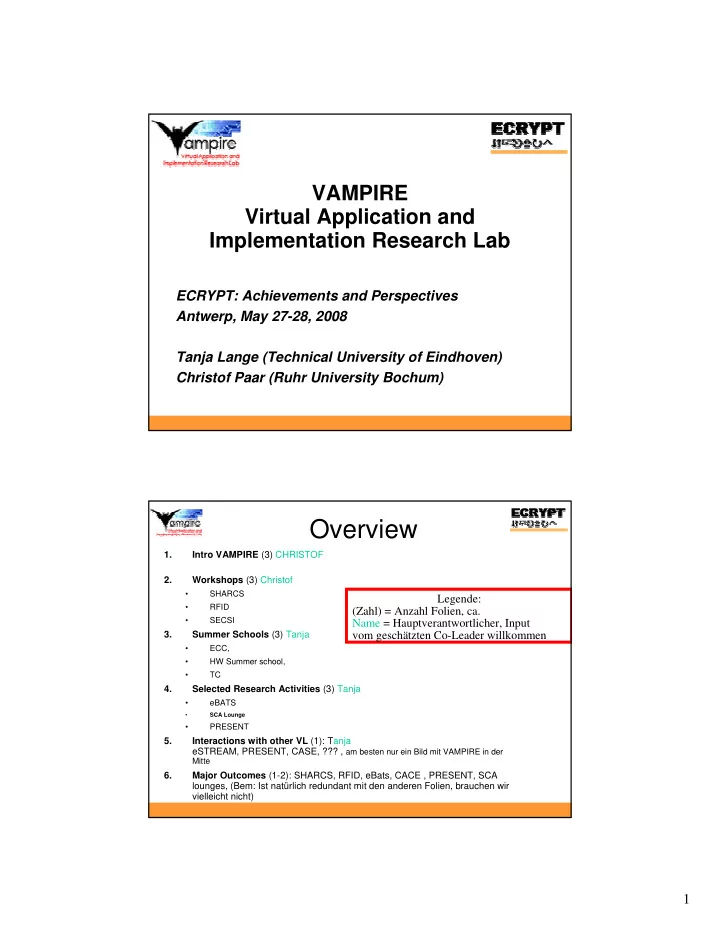
VAMPIRE Virtual Application and Implementation Research Lab
ECRYPT: Achievements and Perspectives Antwerp, May 27-28, 2008 Tanja Lange (Technical University of Eindhoven) Christof Paar (Ruhr University Bochum)
Overview
1. Intro VAMPIRE (3) CHRISTOF 2. Workshops (3) Christof
- SHARCS
- RFID
- SECSI
3. Summer Schools (3) Tanja
- ECC,
- HW Summer school,
- TC
4. Selected Research Activities (3) Tanja
- eBATS
- SCA Lounge
- PRESENT
5. Interactions with other VL (1): Tanja eSTREAM, PRESENT, CASE, ??? , am besten nur ein Bild mit VAMPIRE in der
Mitte
6. Major Outcomes (1-2): SHARCS, RFID, eBats, CACE , PRESENT, SCA lounges, (Bem: Ist natürlich redundant mit den anderen Folien, brauchen wir vielleicht nicht)
Legende: (Zahl) = Anzahl Folien, ca. Name = Hauptverantwortlicher, Input vom geschätzten Co-Leader willkommen