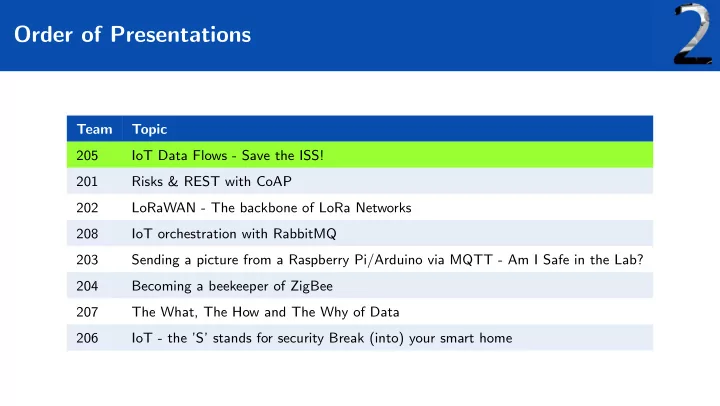
Order of Presentations
Team Topic 205 IoT Data Flows - Save the ISS! 201 Risks & REST with CoAP 202 LoRaWAN - The backbone of LoRa Networks 208 IoT orchestration with RabbitMQ 203 Sending a picture from a Raspberry Pi/Arduino via MQTT - Am I Safe in the Lab? 204 Becoming a beekeeper of ZigBee 207 The What, The How and The Why of Data 206 IoT - the ’S’ stands for security Break (into) your smart home