General Letter Substitution
Algorithm: Substitute 1 letter for another Key Ciphertext: LUGAU
PLAINTEXT LETTER A B C D E F G H I J K L M CIPHERTEXT LETTER G J A O U N E Z Y P H S T PLAINTEXT LETTER N O P Q R S T U V W X Y Z CIPHERTEXT LETTER V W L M I B D C R K F Q X
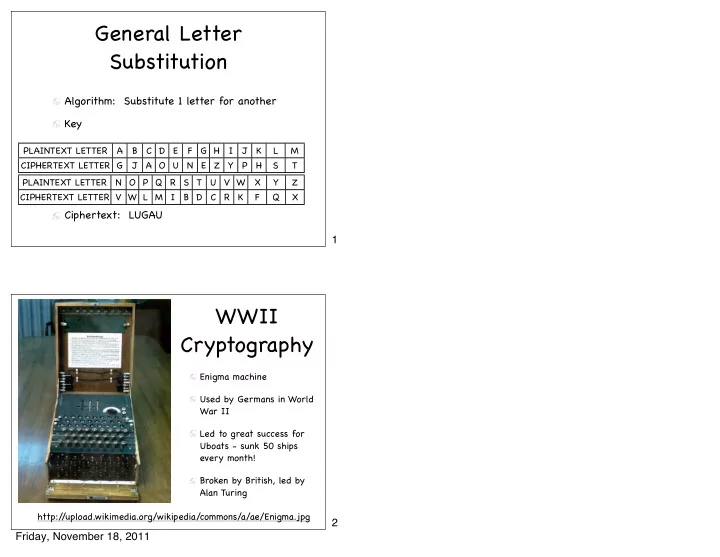
WWII Cryptography
http:/ /upload.wikimedia.org/wikipedia/commons/a/ae/Enigma.jpg Enigma machine Used by Germans in World War II Led to great success for Uboats - sunk 50 ships every month! Broken by British, led by Alan Turing
1 2 Friday, November 18, 2011