CREATE YOUR OWN EXERCISE 1 Outline Team 1: IPv6 Firewalls Team 2: - PowerPoint PPT Presentation
Wave II: Review January 23 rd 2014 CREATE YOUR OWN EXERCISE 1 Outline Team 1: IPv6 Firewalls Team 2: OpenVPN Team 3: CoDel Team 4: Honeypots 2 Thomas Schultz Aneta Stevanovic IPv6 Firewall Testing 3 Reviewing Highlights
Wave II: Review – January 23 rd 2014 CREATE YOUR OWN EXERCISE 1
Outline • Team 1: IPv6 Firewalls • Team 2: OpenVPN • Team 3: CoDel • Team 4: Honeypots 2
Thomas Schultz Aneta Stevanovic IPv6 Firewall Testing 3
Reviewing Highlights • Doing their lab – Storybased workflow – Entertaining prelab questions • Seeing them do our lab – Weaknesses in the lab instructions – Seeing which prelab parts needed more emphasis for doing the exercise => Gain insight into swapped perspectives 4
Exercise Setup Firewall ISP Server Server Server eth1 eth1 eth0 eth0 PC5 PC2 bbbb::2 bbbb::1 cccc::1 cccc::5 mtu=1280 eth0 Web-Server port 80 aaaa::2 SSH-Server port 22 PC3 eth0 aaaa::1 eth0 cccc::4 PC1 PC4 Client Client/ Attacker
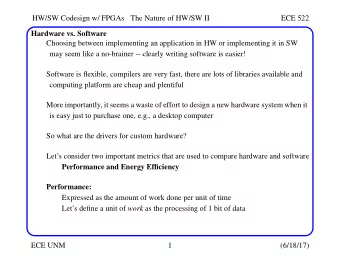
Course of our Lab • Ip6tables script • Webserver • ICMPv6 • Outgoing Traffic • Extension headers • Validation 6
Feedback Highlights • Clear how IPv6 has to be treated differently from Ipv4 • Builds on iptables from ilab1 • Clearly structured ip6tables skeleton script, no misunderstandings where the current task should be inserted • Attack toolkit tests the functionality of the setup well and provides feedback on the success of the penetration attempts 7
Major Points to Improve • Add storyline, small linking sections for better flow • Investigate fragmentation issue in the lab system • Prelab: Improve external references to include more further readings • Summarize security issues in more detail 8
Benjamin Beier and Felix Kuperjans Virtual Private Networks with OpenVPN in restricted environments 9
Reviewing the other team's lab • Felt a bit like being kept under surveillance • Interesting to see a lab in its early stages • Exiciting to run into unforseen problems 10
Observing the other team doing our lab • Extremely difficult to hold one's tongue • Notice problems that you didn't expect • Unforseen interpretations of our guidance 11
The Setup (tm) eth1/10.1.1.1/24 eth1/10.1.1.123/24 OpenVPN HTTP Client A eth0/172.16.0.2/12 Proxy eth0/172.16.0.1/12 eth0/172.16.0.123/12 OpenVPN OpenVPN eth1/10.2.2.1/24 Server Client B eth0/172.16.0.234/12 Private Public eth1/10.2.2.2/24 Netgear Webserver Webserver ● Restricted Network ● The Internet ● Private Network
Course of Your Lab • Set up the networks • Configure the http proxy • Configure the webservers • Get the basic OpenVPN setup running • Circumvent the proxy • Further discussion 13
Highlights of Your Lab • Good prelab ↔ lab coverage • Interesting real-world examples • Clear and precise prelab questions • Highly relevant for practical use cases 14
Major Points to Improve • Reordering some questions • Add links to the prelab and man pages • Be more precise in explanations of complex topics • Add guiding questions to larger tasks 15
Peter Gawronski and Simon Gabl DEFEAT THE LAG
How Did You Like the Reviewing? • Just give a short impression about: – It is very nice to see a short but interesting lab – The expression on the creator's faces when we did something “stupid” is priceless ;) – Tasks take double the time you may think they will do. You underestimate time for reading, research etc. massively when you already know what you want them to do. – Think of wrong turns the reviewer may take – it should work anyway or be verifiable 17
Your Setup 18
Course of Your Lab This pic is huge!!! • Give a 2 minute outline of your lab – Setup of a Bandwidth Throttler (e.g. for real life usage with a “dumb” router) – Try three different queueing mechanisms (the good, the bad and the ugly) – Test their performance in numbers with and watch the buffers bloat – Experience the differences in a real life application: assaultcube, online FPS 19
Highlights of Your Lab • What did your review team like most? – The testing part – you really see the massive improvement in both numbers and game experience – The not so strict mood and a little humor in the lab with a storyline about a real life problem and its solution – CoDel was not the only content but a broader overview over topics 20
Major Points to Improve • What are the major points you will improve? – Questions may seem clear to you but not to someone else, especially look out for instructions which may be misinterpreted – Are you able to do the lab completely with an answer missing or doing it “wrong”? – Maybe add more information to the prelab about tools used – students will have seen it before and can use it easier 21
Benjamin Braun, Klemens Mang Securing networks with Honeypots
How Did You Like the Reviewing? • Highlights as reviewer – The lab looked very complete, sophisticated and with a nice level of difficulty – In some parts of the lab some additional guidance would be appreciated to speed up the progress • Highlights as reviewed team – Students do not read every part of the lab and therefore key information should be particularly highlighted – Students actually do the lab in more complicated way than you would actually expected them to do 23
Lab Setup Ubuntu eth3/10.0.1.20/24 Honeyd PC3 PC6 eth0/10.0.1.0/28 (DHCP) Server PC5 PC2 eth0/10.0.1.254/24 Router eth0/10.0.2.2/28 eth1/10.0.2.2/28 Attacker PC1 PC4 Switch
Course of Your Lab • Install Ubuntu and do the cabling • Deploy a basic honeypot configuration for a particular personality and fake service • Explore a pre-defined network topology and find a specific target host • With the help of fingerprints and portscans try to distinguish the real host from honeypots • Do a honeypot log analysis and further thinking 25
Highlights of Your Lab • The reviewers particularly enjoyed the interactivity of the honeynet exploration • The creativity of the virtual hosts in the exploration part caught the reviewers ’ interest • The questions about thinking further were enjoyed 26
Major Points to Improve • The deployment scripts and the overall lab should be made more robust • The most important instructions should be highlighted more clearly and references to the PreLab should be made when appropriate • Important debugging information should be provided when appropriate • Provide a better storyline and practical outlook 27
Recommend
More recommend
Explore More Topics
Stay informed with curated content and fresh updates.