Authorization in Object-oriented Databases
Anna Vapen David Hall December 2008
Authorization
- ”the permission or power given to sb to do sth:
enter a security area without authorization”
Oxford Advanced Learner's Dictionary
- authorization is the concept of allowing access to
resources only to those permitted to use them.
“Authorization.” Wikipedia, The Free Encyc
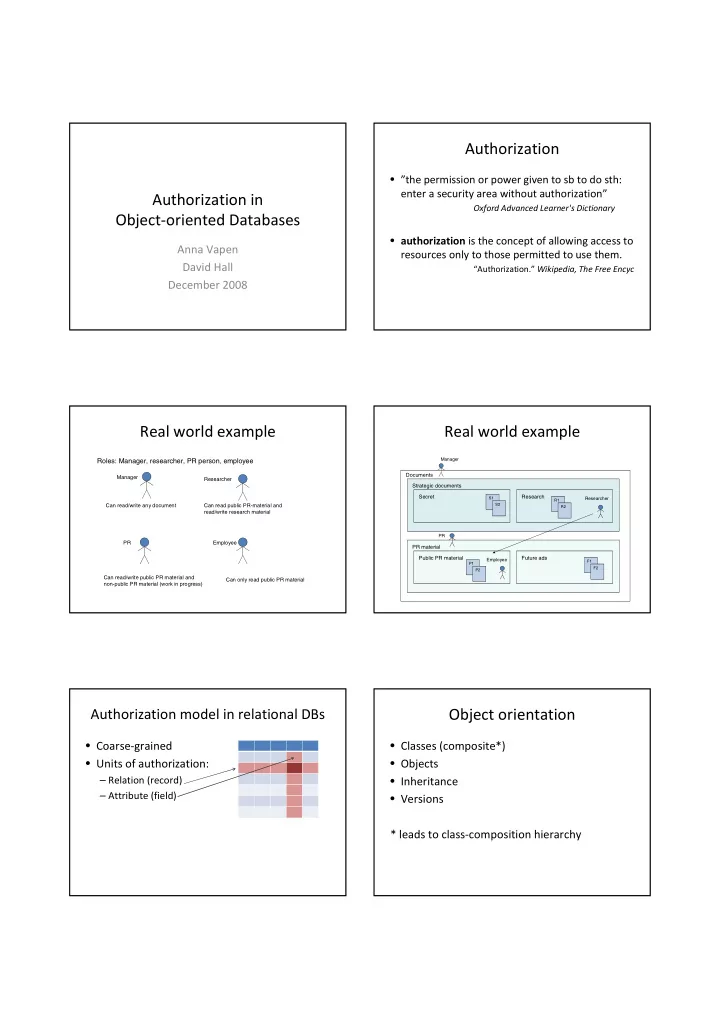
Real world example
Manager PR Researcher
Roles: Manager, researcher, PR person, employee
Employee Can read/write any document Can read public PR-material and read/write research material Can read/write public PR material and non-public PR material (work in progress) Can only read public PR material
Real world example
Documents Strategic documents Secret PR material Research Public PR material Future ads
Manager Researcher Employee PR
S1 S2 R1 R2 F1 F2 P1 P2
Authorization model in relational DBs
- Coarse-grained
- Units of authorization:
– Relation (record) – Attribute (field)
Object orientation
- Classes (composite*)
- Objects
- Inheritance
- Versions