5/30/2017 1
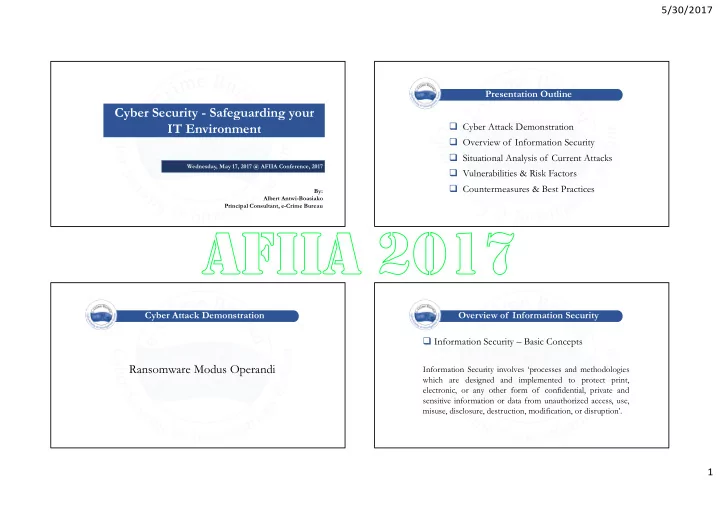
Wednesday, May 17, 2017 @ AFIIA Conference, 2017Cyber Security - Safeguarding your IT Environment
By: Albert Antwi-Boasiako Principal Consultant, e-Crime BureauPresentation Outline Cyber Attack Demonstration Overview of Information Security Situational Analysis of Current Attacks Vulnerabilities & Risk Factors Countermeasures & Best Practices Cyber Attack Demonstration
Ransomware Modus Operandi
Overview of Information Security
Information Security involves ‘processes and methodologies which are designed and implemented to protect print, electronic, or any other form of confidential, private and sensitive information or data from unauthorized access, use, misuse, disclosure, destruction, modification, or disruption’.
Information Security – Basic Concepts