1
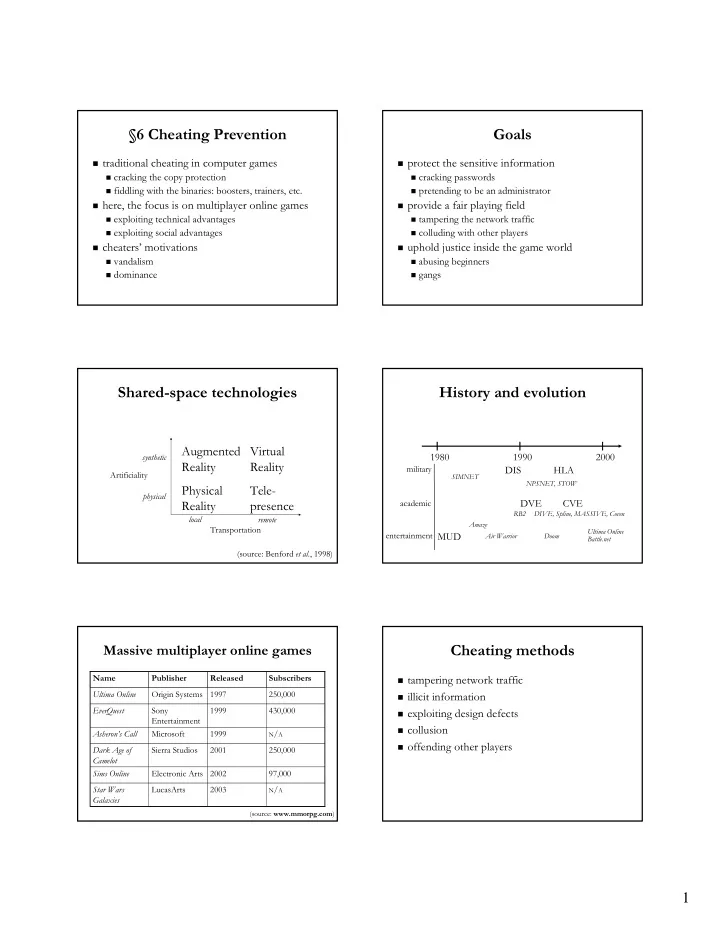
§6 Cheating Prevention
traditional cheating in computer games
cracking the copy protection fiddling with the binaries: boosters, trainers, etc.
here, the focus is on multiplayer online games
exploiting technical advantages exploiting social advantages
cheaters’ motivations
vandalism dominance
Goals
protect the sensitive information
cracking passwords pretending to be an administrator
provide a fair playing field
tampering the network traffic colluding with other players
uphold justice inside the game world
abusing beginners gangs
Shared-space technologies
Augmented Reality Virtual Reality Physical Reality Tele- presence
Transportation Artificiality local remote synthetic physical (source: Benford et al., 1998)
History and evolution
1980 1990 2000
SIMNET
DIS HLA DVE CVE
DIVE, Spline, MASSIVE, Coven NPSNET, STOW
military academic entertainment
Amaze RB2 Doom
MUD
Battle.net Ultima Online Air Warrior
Massive multiplayer online games
N/A
2003 LucasArts Star Wars Galaxies 97,000 2002 Electronic Arts Sims Online 250,000 2001 Sierra Studios Dark Age of Camelot
N/A
1999 Microsoft Asheron’s Call 430,000 1999 Sony Entertainment EverQuest 250,000 1997 Origin Systems Ultima Online Subscribers Released Publisher Name
(source: www.mmorpg.com)
Cheating methods
tampering network traffic illicit information exploiting design defects collusion
- ffending other players