Elements of Computing Systems, Nisan & Schocken, MIT Press, www.nand2tetris.org , Chapter 7: Virutal Machine, Part I slide 25
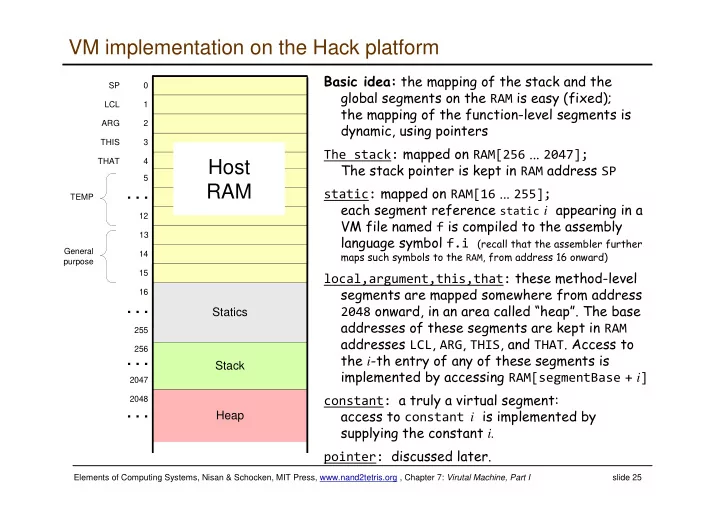
VM implementation on the Hack platform
( "RAM '(C (( ! '+ The stack: RAM[256 ###2047]; RAM SP static: RAM[16 ###255]; (static i (f "' '"f.i "(
'"RAM+(=>%
local,argument,this,that: ! %( 2048 %+45#" (RAM LCL+ARG+THIS+THAT# i '('( "'RAM[segmentBase + i] constant: '! constant i "' 'i. pointer: #
Statics
3 12
. . .
4 5 14 15 1 13 2 THIS THAT SP LCL ARG TEMP 255
. . .
16 General purpose 2047
. . .
256 2048