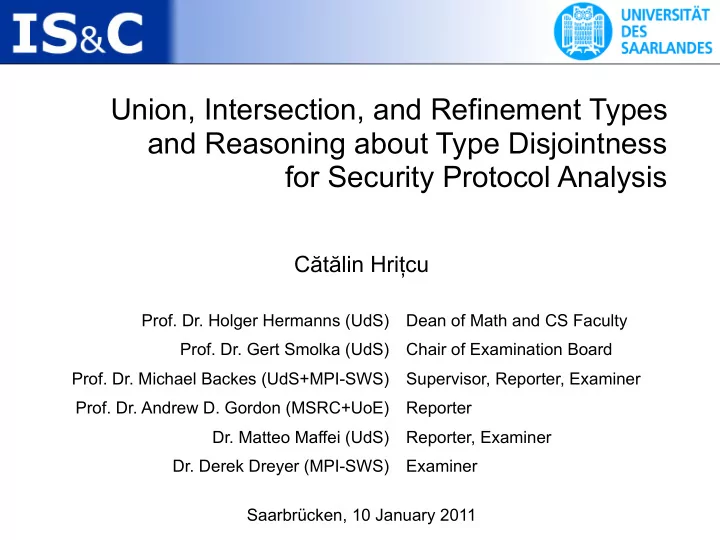
Union, Intersection, and Refinement Types and Reasoning about Type Disjointness for Security Protocol Analysis
Saarbrücken, 10 January 2011
Cătălin Hrițcu
- Prof. Dr. Holger Hermanns (UdS)
- Prof. Dr. Gert Smolka (UdS)
- Prof. Dr. Michael Backes (UdS+MPI-SWS)
- Prof. Dr. Andrew D. Gordon (MSRC+UoE)
- Dr. Matteo Maffei (UdS)
- Dr. Derek Dreyer (MPI-SWS)
Dean of Math and CS Faculty Chair of Examination Board Supervisor, Reporter, Examiner Reporter Reporter, Examiner Examiner