1
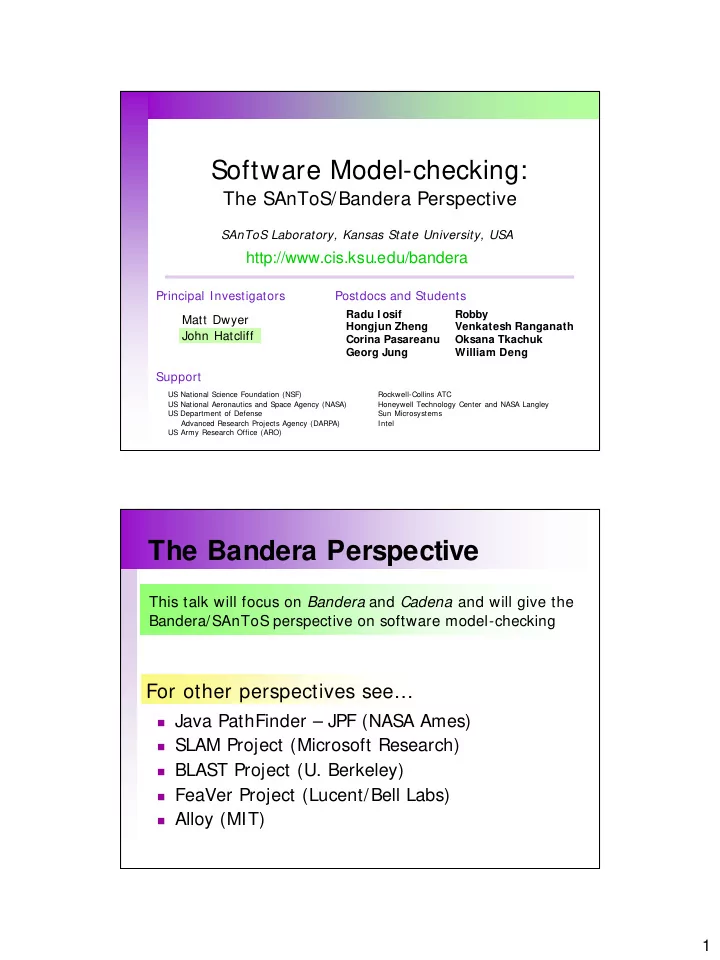
Software Model-checking:
The SAnToS/Bandera Perspective
http://www.cis.ksu.edu/bandera
Matt Dwyer John Hatcliff Principal Investigators Support
US National Science Foundation (NSF) US National Aeronautics and Space Agency (NASA) US Department of Defense Advanced Research Projects Agency (DARPA) US Army Research Office (ARO) Rockwell-Collins ATC Honeywell Technology Center and NASA Langley Sun Microsystems Intel
SAnToS Laboratory, Kansas State University, USA Postdocs and Students
Radu I osif Hongjun Zheng Corina Pasareanu Georg Jung Robby Venkatesh Ranganath Oksana Tkachuk William Deng
The Bandera Perspective
Java PathFinder – JPF (NASA Ames) SLAM Project (Microsoft Research) BLAST Project (U. Berkeley) FeaVer Project (Lucent/Bell Labs) Alloy (MIT)
This talk will focus on Bandera and Cadena and will give the Bandera/SAnToS perspective on software model-checking