Security Threats in Vehicular Ad Hoc Networks
Ahmed Shoeb Al Hasan1, Md. Shohrab Hossain1, and Mohammed Atiquzzaman2
1Department of Computer Science & Engineering, Bangladesh University of Engineering & Technology, Dhaka, Bangladesh 2School of Computer Science, University of Oklahoma, Norman, OK 73019, USA
Email: shoeb.al.hasan@gmail.com, mshohrabhossain@cse.buet.ac.bd, atiq@ou.edu
Abstract— A new type of Mobile Ad Hoc Network (MANET) is Vehicular Ad Hoc Network (VANET) that allows smart transport system to provide road security and reduce traffic jam through automobile to automobile and automobile to roadside
- communication. However, security issues for VANETs have
become a major concern for researchers. VANET is different from other ad hoc networks due to its dynamic topology and mixed structural design. Hence, designing security schemes to authenticate broadcasted messages and discard malicious messages are crucial in VANETs. Here, at first we identify various security issues for VANET and discuss possible defense mechanisms to mitigate those threats. We then classify the defense mechanisms into major categories and critically analyze them based on different performance criteria. Finally, we list several open research issues related to VANET security to inspire researchers to work on these open problems and propose solutions towards efficient trust organization in VANET. Keywords—Vehicular Ad Hoc Network, VANET, Mobile Ad Hoc Network, MANET, Cryptography, V2V communication, Security Threat.
- I. INTRODUCTION
VANETs are a subgroup
- f
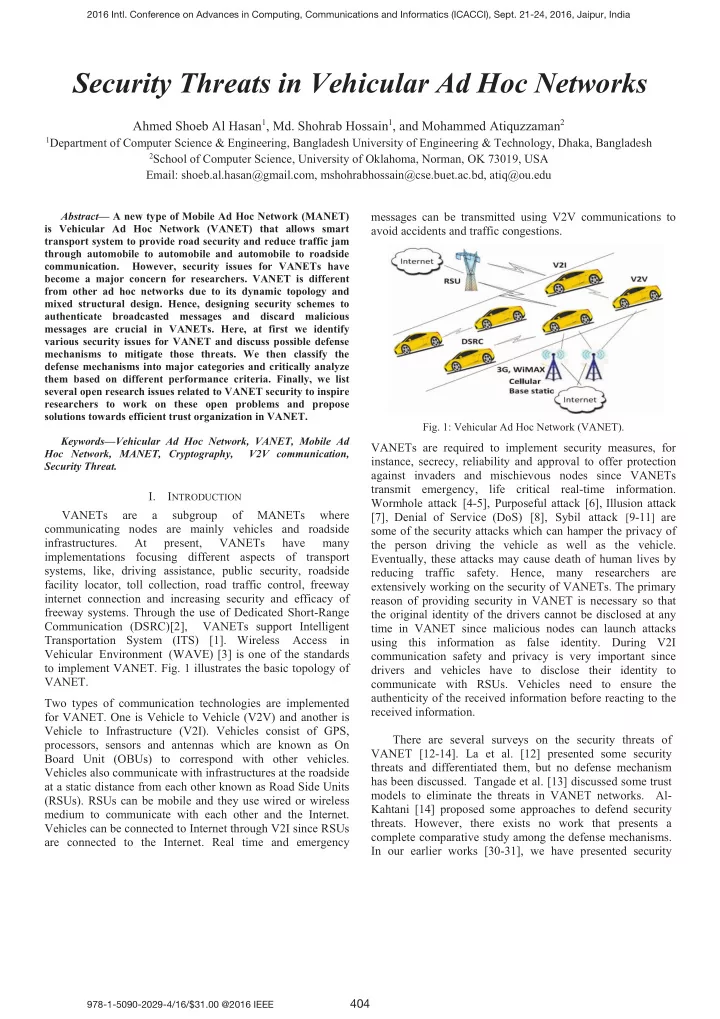
MANETs where communicating nodes are mainly vehicles and roadside infrastructures. At present, VANETs have many implementations focusing different aspects of transport systems, like, driving assistance, public security, roadside facility locator, toll collection, road traffic control, freeway internet connection and increasing security and efficacy of freeway systems. Through the use of Dedicated Short-Range Communication (DSRC)[2], VANETs support Intelligent Transportation System (ITS) [1]. Wireless Access in Vehicular Environment (WAVE) [3] is one of the standards to implement VANET. Fig. 1 illustrates the basic topology of VANET. Two types of communication technologies are implemented for VANET. One is Vehicle to Vehicle (V2V) and another is Vehicle to Infrastructure (V2I). Vehicles consist of GPS, processors, sensors and antennas which are known as On Board Unit (OBUs) to correspond with other vehicles. Vehicles also communicate with infrastructures at the roadside at a static distance from each other known as Road Side Units (RSUs). RSUs can be mobile and they use wired or wireless medium to communicate with each other and the Internet. Vehicles can be connected to Internet through V2I since RSUs are connected to the Internet. Real time and emergency messages can be transmitted using V2V communications to avoid accidents and traffic congestions.
- Fig. 1: Vehicular Ad Hoc Network (VANET).
VANETs are required to implement security measures, for instance, secrecy, reliability and approval to offer protection against invaders and mischievous nodes since VANETs transmit emergency, life critical real-time information. Wormhole attack [4-5], Purposeful attack [6], Illusion attack [7], Denial of Service (DoS) [8], Sybil attack [9-11] are some of the security attacks which can hamper the privacy of the person driving the vehicle as well as the vehicle. Eventually, these attacks may cause death of human lives by reducing traffic safety. Hence, many researchers are extensively working on the security of VANETs. The primary reason of providing security in VANET is necessary so that the original identity of the drivers cannot be disclosed at any time in VANET since malicious nodes can launch attacks using this information as false identity. During V2I communication safety and privacy is very important since drivers and vehicles have to disclose their identity to communicate with RSUs. Vehicles need to ensure the authenticity of the received information before reacting to the received information. There are several surveys on the security threats of VANET [12-14]. La et al. [12] presented some security threats and differentiated them, but no defense mechanism has been discussed. Tangade et al. [13] discussed some trust models to eliminate the threats in VANET networks. Al- Kahtani [14] proposed some approaches to defend security
- threats. However, there exists no work that presents a
complete comparative study among the defense mechanisms. In our earlier works [30-31], we have presented security
2016 Intl. Conference on Advances in Computing, Communications and Informatics (ICACCI), Sept. 21-24, 2016, Jaipur, India 978-1-5090-2029-4/16/$31.00 @2016 IEEE
404