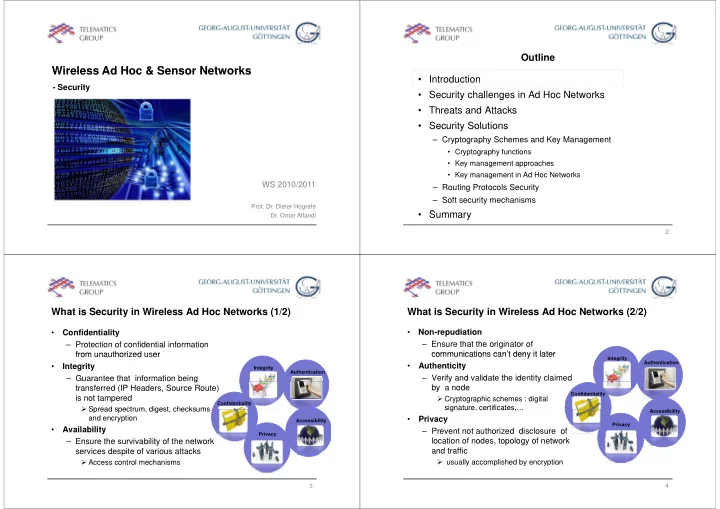
Wireless Ad Hoc & Sensor Networks Wireless Ad Hoc & Sensor Networks
- Security
WS 2010/2011 WS 2010/2011
- Prof. Dr. Dieter Hogrefe
- Dr. Omar Alfandi
Outline
- Introduction
- Security challenges in Ad Hoc Networks
y g
- Threats and Attacks
- Security Solutions
Security Solutions
– Cryptography Schemes and Key Management
- Cryptography functions
yp g p y
- Key management approaches
- Key management in Ad Hoc Networks
– Routing Protocols Security – Soft security mechanisms
S
- Summary
2
What is Security in Wireless Ad Hoc Networks (1/2)
- Confidentiality
– Protection of confidential information from unauthorized user
v
Integrity Authentication
from unauthorized user
- Integrity
– Guarantee that information being
v
Confidentiality
g transferred (IP Headers, Source Route) is not tampered
- Spread spectrum digest checksums
Privacy Accessibility
- Spread spectrum, digest, checksums
and encryption
- Availability
– Ensure the survivability of the network services despite of various attacks
- Access control mechanisms
3
What is Security in Wireless Ad Hoc Networks (2/2)
- Non-repudiation
– Ensure that the originator of communications can’t deny it later
v
Integrity Authentication
communications can t deny it later
- Authenticity
– Verify and validate the identity claimed
Confidentiality A ibilit
y y by a node
- Cryptographic schemes : digital
signature, certificates,…
Privacy Accessibility
signature, certificates,…
- Privacy
– Prevent not authorized disclosure of location of nodes, topology of network and traffic
- usually accomplished by encryption
y p y yp
4