Introduction to Cryptography
Security Protocols
Jim Royer October 9, 2018
Crypto ❖ Security Protocols 1
References
◮ ”Key Establishment,” Chapter 13 of Understanding Cryptography by Paar & Pelzl ◮ Wide Mouth Frog Protocol from Wikipedia
https://en.wikipedia.org/wiki/Wide_Mouth_Frog_protocol
◮ Explain like I’m 5: Kerberos by Lynn Root
http://www.roguelynn.com/words/explain-like-im-5-kerberos/
◮ Secure Electronic Transaction from Wikipedia
https://en.wikipedia.org/wiki/Secure_Electronic_Transaction
Crypto ❖ Security Protocols 2
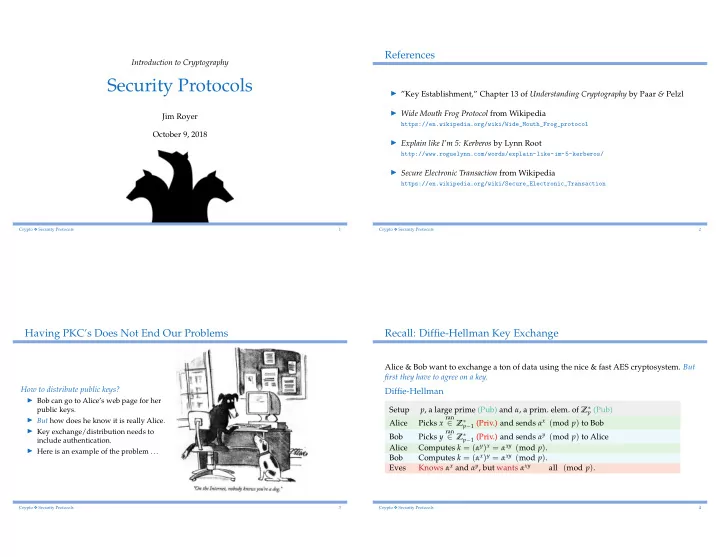
Having PKC’s Does Not End Our Problems
How to distribute public keys? ◮ Bob can go to Alice’s web page for her
public keys. ◮ But how does he know it is really Alice. ◮ Key exchange/distribution needs to include authentication. ◮ Here is an example of the problem ...
Crypto ❖ Security Protocols 3
Recall: Diffie-Hellman Key Exchange
Alice & Bob want to exchange a ton of data using the nice & fast AES cryptosystem. But first they have to agree on a key.
Diffie-Hellman
Setup p, a large prime (Pub) and α, a prim. elem. of Z∗
p (Pub)
Alice Picks x
ran
∈ Z∗
p−1 (Priv.) and sends αx (mod p) to Bob
Bob Picks y
ran
∈ Z∗
p−1 (Priv.) and sends αy (mod p) to Alice
Alice Computes k = (αy)x = αxy (mod p). Bob Computes k = (αx)y = αxy (mod p). Eves Knows αx and αy, but wants αxy all (mod p).
Crypto ❖ Security Protocols 4