Security and Privacy in the Smart Energy Grid Martin Erich Jobst - PowerPoint PPT Presentation
Security and Privacy in the Smart Energy Grid Martin Erich Jobst Chair for Network Architectures and Services Department for Computer Science Technische Universit at M unchen July 01, 2013 Martin Erich Jobst: Security and Privacy in the
Security and Privacy in the Smart Energy Grid Martin Erich Jobst Chair for Network Architectures and Services Department for Computer Science Technische Universit¨ at M¨ unchen July 01, 2013 Martin Erich Jobst: Security and Privacy in the Smart Energy Grid 1
Motivation Smart energy grids offer many new features for both customers and electricity providers Collection of real-time consumption data Capacity-dependent regulation of smart appliances Load-dependent regulation of small power plants Remote management of electricity meters However, there are great privacy and security concerns Invasion of customer privacy Energy theft Attacks on the customer Sabotage of the power grid Martin Erich Jobst: Security and Privacy in the Smart Energy Grid 2
Motivation Smart energy grids offer many new features for both customers and electricity providers Collection of real-time consumption data Capacity-dependent regulation of smart appliances Load-dependent regulation of small power plants Remote management of electricity meters However, there are great privacy and security concerns Invasion of customer privacy Energy theft Attacks on the customer Sabotage of the power grid Martin Erich Jobst: Security and Privacy in the Smart Energy Grid 2
Outline 1 Background 2 Privacy Concerns Solutions 3 Security Threats Countermeasures Martin Erich Jobst: Security and Privacy in the Smart Energy Grid 3
Smart Meters Customer Premises Installation (integrated or separate) SML, DLMS/COSEM or IEC 61850 to provider S0-Interface or internal Metering Device Home Gateway to customer Martin Erich Jobst: Security and Privacy in the Smart Energy Grid 4
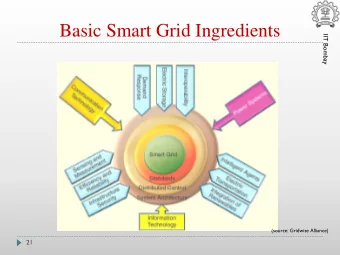
Smart Energy Grid Smart Meter Households Metering Backend Power Plant Provider Network Data Aggregator/ Concentartor Martin Erich Jobst: Security and Privacy in the Smart Energy Grid 5
Smart metering regulations in the EU EU: “At least 80 % of consumers shall be equipped with intelligent metering systems by 2020.” (directives 2006/32/EC and 2009/72/EC) Germany: mandatory for new installations ( § 21d EnWG, MessZV) Requirements: Measurement Instruments Directive (MID) 2004 However, only abstract requirements for the implementation (certain accuracy and be tamper-resistant ) More detailed requirements are exclusive to a growing number of international standards (ISO, IEC, EN, etc.) Martin Erich Jobst: Security and Privacy in the Smart Energy Grid 6
Smart metering regulations in the EU EU: “At least 80 % of consumers shall be equipped with intelligent metering systems by 2020.” (directives 2006/32/EC and 2009/72/EC) Germany: mandatory for new installations ( § 21d EnWG, MessZV) Requirements: Measurement Instruments Directive (MID) 2004 However, only abstract requirements for the implementation (certain accuracy and be tamper-resistant ) More detailed requirements are exclusive to a growing number of international standards (ISO, IEC, EN, etc.) Martin Erich Jobst: Security and Privacy in the Smart Energy Grid 6
Outline 1 Background 2 Privacy Concerns Solutions 3 Security Threats Countermeasures Martin Erich Jobst: Security and Privacy in the Smart Energy Grid 7
Privacy Example smart meter measurement data, redrawn from actual measurements Martin Erich Jobst: Security and Privacy in the Smart Energy Grid 8
Privacy cont. Measurement interval: as low as 2 sec Questions that may be answered: What kind of devices do you use (maybe manufacturer, model)? When are you at home? When do you wake up or go to bed (to the minute)? How well do you sleep at night (light on/off)? Are you on sick leave (and do you spend it at home)? and many more Research: Possible to determine what you watch on TV (black/white contrast from LCD backlight) Martin Erich Jobst: Security and Privacy in the Smart Energy Grid 9
Privacy cont. Measurement interval: as low as 2 sec Questions that may be answered: What kind of devices do you use (maybe manufacturer, model)? When are you at home? When do you wake up or go to bed (to the minute)? How well do you sleep at night (light on/off)? Are you on sick leave (and do you spend it at home)? and many more Research: Possible to determine what you watch on TV (black/white contrast from LCD backlight) Martin Erich Jobst: Security and Privacy in the Smart Energy Grid 9
Privacy cont. Measurement interval: as low as 2 sec Questions that may be answered: What kind of devices do you use (maybe manufacturer, model)? When are you at home? When do you wake up or go to bed (to the minute)? How well do you sleep at night (light on/off)? Are you on sick leave (and do you spend it at home)? and many more Research: Possible to determine what you watch on TV (black/white contrast from LCD backlight) Martin Erich Jobst: Security and Privacy in the Smart Energy Grid 9
Outline 1 Background 2 Privacy Concerns Solutions 3 Security Threats Countermeasures Martin Erich Jobst: Security and Privacy in the Smart Energy Grid 10
Privacy Solutions I The obvious approach . . . is to increase the interval between reports Pros Easy to implement Guaranteed protection (depending on the interval) Customer regains full local access Cons Less accurate information for provider Conclusion Feasible short-term alternative May be combined with anonymization (frequent anonymized and infrequent attributabe reports) Martin Erich Jobst: Security and Privacy in the Smart Energy Grid 11
Privacy Solutions I The obvious approach . . . is to increase the interval between reports Pros Easy to implement Guaranteed protection (depending on the interval) Customer regains full local access Cons Less accurate information for provider Conclusion Feasible short-term alternative May be combined with anonymization (frequent anonymized and infrequent attributabe reports) Martin Erich Jobst: Security and Privacy in the Smart Energy Grid 11
Privacy Solutions I The obvious approach . . . is to increase the interval between reports Pros Easy to implement Guaranteed protection (depending on the interval) Customer regains full local access Cons Less accurate information for provider Conclusion Feasible short-term alternative May be combined with anonymization (frequent anonymized and infrequent attributabe reports) Martin Erich Jobst: Security and Privacy in the Smart Energy Grid 11
Privacy Solutions I The obvious approach . . . is to increase the interval between reports Pros Easy to implement Guaranteed protection (depending on the interval) Customer regains full local access Cons Less accurate information for provider Conclusion Feasible short-term alternative May be combined with anonymization (frequent anonymized and infrequent attributabe reports) Martin Erich Jobst: Security and Privacy in the Smart Energy Grid 11
Privacy Solutions II The pseudo-approach . . . is pseudonymize reports by a data aggregator or TTP Pros Accurate anonymous readings Cons Requires trusted point (where?) Still identifiable by collecting external information Conclusion Not such a good idea ;) Martin Erich Jobst: Security and Privacy in the Smart Energy Grid 12
Privacy Solutions II The pseudo-approach . . . is pseudonymize reports by a data aggregator or TTP Pros Accurate anonymous readings Cons Requires trusted point (where?) Still identifiable by collecting external information Conclusion Not such a good idea ;) Martin Erich Jobst: Security and Privacy in the Smart Energy Grid 12
Privacy Solutions II The pseudo-approach . . . is pseudonymize reports by a data aggregator or TTP Pros Accurate anonymous readings Cons Requires trusted point (where?) Still identifiable by collecting external information Conclusion Not such a good idea ;) Martin Erich Jobst: Security and Privacy in the Smart Energy Grid 12
Privacy Solutions II The pseudo-approach . . . is pseudonymize reports by a data aggregator or TTP Pros Accurate anonymous readings Cons Requires trusted point (where?) Still identifiable by collecting external information Conclusion Not such a good idea ;) Martin Erich Jobst: Security and Privacy in the Smart Energy Grid 12
Privacy Solutions III The statistical approach . . . is to aggregate (or simply sum) measurements Pros Easy to implement Good protection (depending on the number) Cons Only usable for overall statistics Also needs TTP (who?) Conclusion Not easy for customers or providers to accept Martin Erich Jobst: Security and Privacy in the Smart Energy Grid 13
Privacy Solutions III The statistical approach . . . is to aggregate (or simply sum) measurements Pros Easy to implement Good protection (depending on the number) Cons Only usable for overall statistics Also needs TTP (who?) Conclusion Not easy for customers or providers to accept Martin Erich Jobst: Security and Privacy in the Smart Energy Grid 13
Privacy Solutions III The statistical approach . . . is to aggregate (or simply sum) measurements Pros Easy to implement Good protection (depending on the number) Cons Only usable for overall statistics Also needs TTP (who?) Conclusion Not easy for customers or providers to accept Martin Erich Jobst: Security and Privacy in the Smart Energy Grid 13
Recommend
More recommend
Explore More Topics
Stay informed with curated content and fresh updates.