Securing Internet Routing
Jobtalk
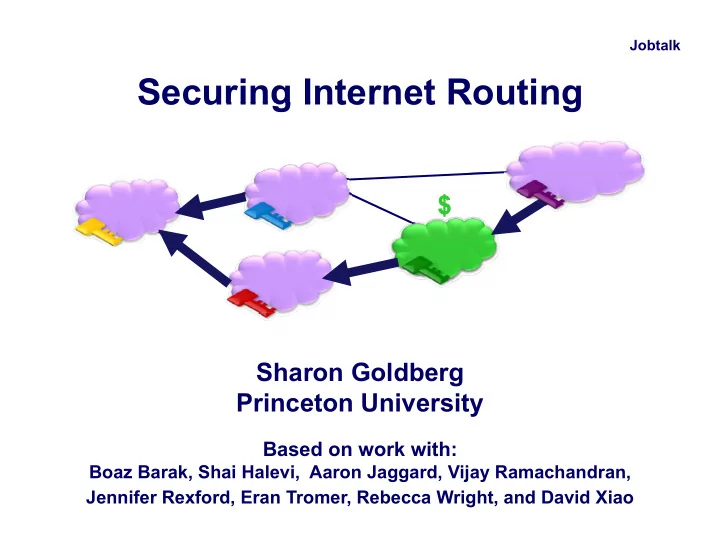
Securing Internet Routing
Local
$
ISP
Sharon Goldberg g Princeton University
Based on work with:
Princeton University
Based on work with:
Boaz Barak, Shai Halevi, Aaron Jaggard, Vijay Ramachandran, Jennifer Rexford, Eran Tromer, Rebecca Wright, and David Xiao