1
www.compaq.com
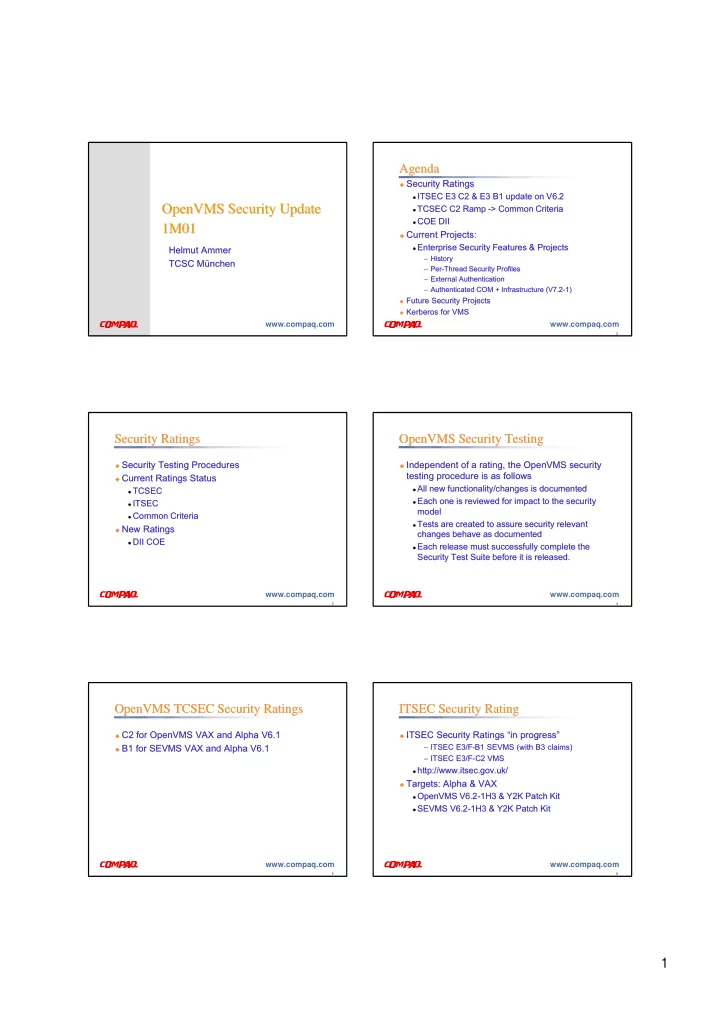
OpenVMS Security OpenVMS Security Update Update 1M01 1M01
Helmut Ammer Helmut Ammer TCSC München TCSC München
2
www.compaq.com
Security Ratings
Security Ratings
ITSEC E3
ITSEC E3 C2 & E3 B1 update on C2 & E3 B1 update on V6 V6.2 .2
TCSEC C2 Ramp
TCSEC C2 Ramp -
- > Common
> Common Criteria Criteria
COE DII
COE DII
Current Projects:
Current Projects:
Enterprise Security Features & Projects
Enterprise Security Features & Projects
– – History History – – Per Per-
- Thread Security Profiles
Thread Security Profiles – – External Authentication External Authentication – – Authenticated COM + Infrastructure (V7.2 Authenticated COM + Infrastructure (V7.2-
- 1)
1)
Future Security
Future Security Projects Projects
Kerberos
Kerberos for VMS for VMS
Agenda Agenda
3
www.compaq.com
Security Ratings Security Ratings
Security Testing Procedures
Security Testing Procedures
Current Ratings Status
Current Ratings Status
TCSEC
TCSEC
ITSEC
ITSEC
Common Criteria
Common Criteria
New Ratings
New Ratings
DII COE
DII COE
4
www.compaq.com
OpenVMS Security Testing OpenVMS Security Testing
Independent of a rating, the OpenVMS security
Independent of a rating, the OpenVMS security testing procedure is as follows testing procedure is as follows
All new functionality/changes is documented
All new functionality/changes is documented
Each one is reviewed for impact to the security
Each one is reviewed for impact to the security model model
Tests are created to assure security relevant
Tests are created to assure security relevant changes behave as documented changes behave as documented
Each release must successfully complete the
Each release must successfully complete the Security Test Suite before it is released. Security Test Suite before it is released.
5
www.compaq.com
OpenVMS TCSEC Security Ratings OpenVMS TCSEC Security Ratings
C2 for OpenVMS VAX and Alpha V6.1
C2 for OpenVMS VAX and Alpha V6.1
B1 for SEVMS VAX and Alpha V6.1
B1 for SEVMS VAX and Alpha V6.1
6
www.compaq.com
ITSEC Security Rating ITSEC Security Rating
ITSEC Security Ratings “in progress”
ITSEC Security Ratings “in progress”
– – ITSEC E3/F ITSEC E3/F-
- B1 SEVMS (with B3 claims)
B1 SEVMS (with B3 claims) – – ITSEC E3/F ITSEC E3/F-
- C2 VMS
C2 VMS
http://www.itsec.gov.uk/
http://www.itsec.gov.uk/
Targets: Alpha & VAX
Targets: Alpha & VAX
OpenVMS V6.2
OpenVMS V6.2-
- 1H3 & Y2K Patch Kit
1H3 & Y2K Patch Kit
SEVMS V6.2
SEVMS V6.2-
- 1H3 & Y2K Patch Kit