1
Non-Malleable Primitives Why and How
The case of Commitments
Rafail Ostrovsky (UCLA, USA) Giuseppe Persiano (Univ. Salerno – ITALY) Ivan Visconti (Univ. Salerno – ITALY)
2
Non-Malleable Primitives Why and How The case of Commitments - - PDF document
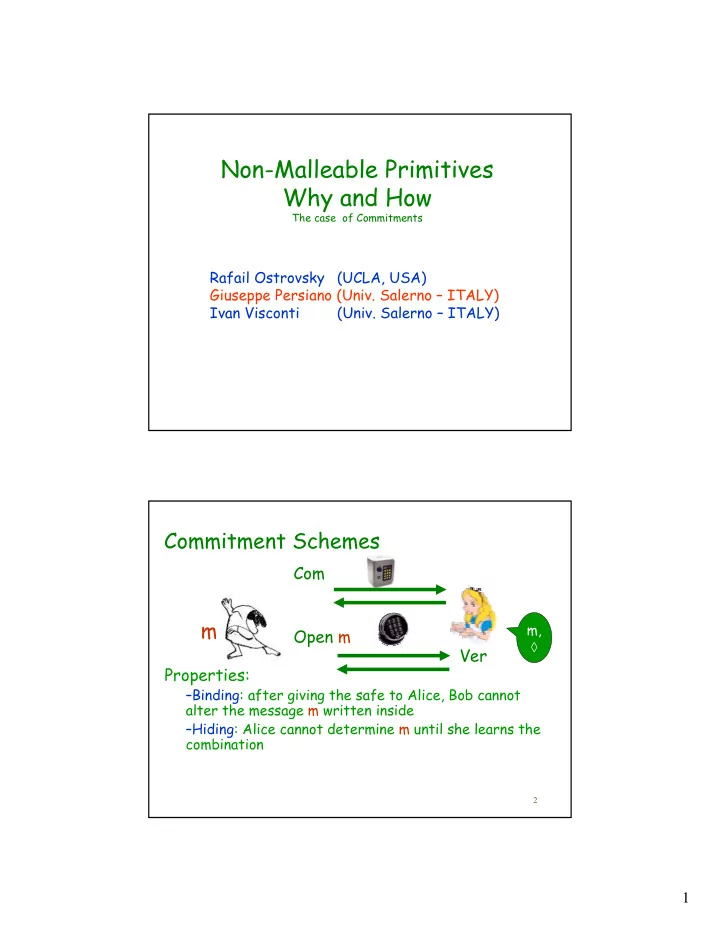
Non-Malleable Primitives Why and How The case of Commitments Rafail Ostrovsky (UCLA, USA) Giuseppe Persiano (Univ. Salerno ITALY) Ivan Visconti (Univ. Salerno ITALY) Commitment Schemes Com m m, Open m Ver Properties:
The case of Commitments
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
Commitment Phase: CR send a statistically binding commitment of m CR use a statistical NMZK argument of knowledge for proving knowledge of the committed message Decommitment Phase: CR send m CR use a statistical NMZK argument of knowledge for proving that m is the committed message Simulator: it commits to junk and uses twice the simulator of the NMZK argument
30
Commitment Phase: CR send a statistically binding commitment of m CR use a statistical NMZK argument of knowledge for proving knowledge of the committed message Decommitment Phase: CR send m CR use a statistical NMZK argument of knowledge for proving that m is the committed message Simulator: it commits to junk and uses twice the simulator of the NMZK argument
31
Commitment Phase: CR send a statistically binding commitment of m CR use a statistical NMZK argument of knowledge for proving knowledge of the committed message Decommitment Phase: CR send m CR use a statistical NMZK argument of knowledge for proving that m is the committed message m Simulator: it commits to junk and uses twice the simulator of the NMZK argument
32
33
34
35
36
37
38
39
Consider the Game ALPHA where the honest committer commits and opens <m1>. Let <m1’> be the openings of the MIM. Consider the Hybrid Game BETA where the simulator commits to junk and
Consider the Hybrid Game GAMMA where the simulator commits to junk and
Consider the Game DELTA where the honest committer commits and opens <m2>. By hybrid arguments we have that the MIM will still open <m1’>. Therefore thus ALPHA and DELTA are indistinguishable and the openings of the MIM do not depend on <m1> and <m2>
40
We have secure auctions on the Internet. Security against man-in-the-middle attacks for commitment
Constant-Round protocols in the plain model are hard to
We have shown a constant-round concurrent non-malleable
It can also be instanced to be statistically hiding (more work
There still are open problems: