1
26/4-07 Datakommunikation - Jonny Pettersson, UmU
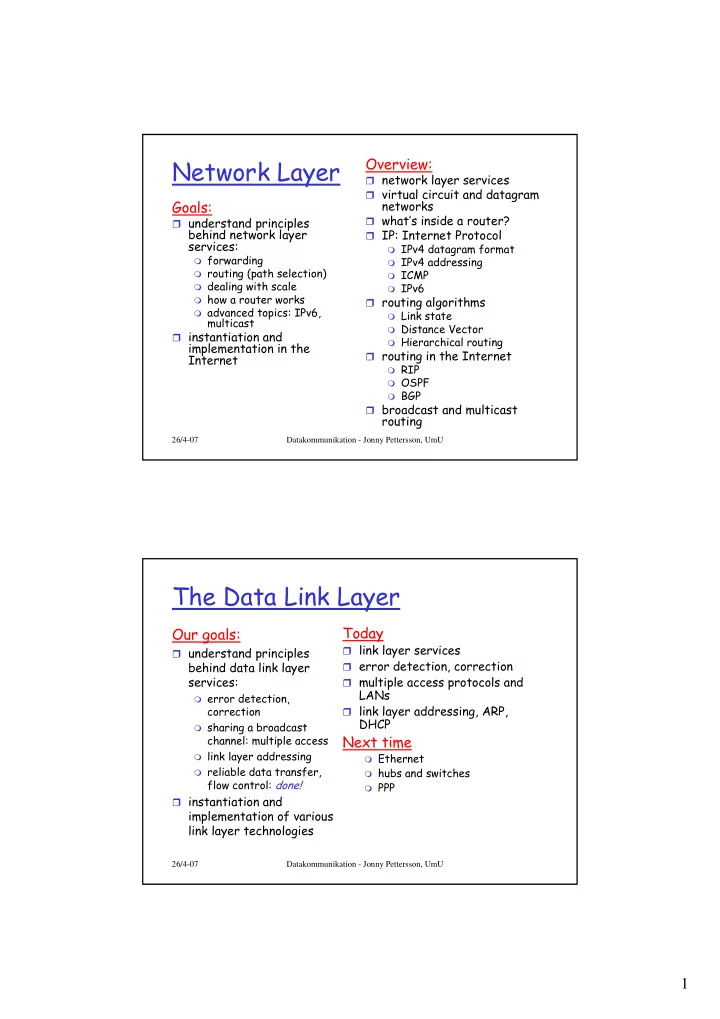
Network Layer
Goals:
understand principles
behind network layer services:
forwarding routing (path selection) dealing with scale how a router works advanced topics: IPv6,
multicast instantiation and
implementation in the Internet
Overview:
network layer services virtual circuit and datagram
networks
what’s inside a router? IP: Internet Protocol
IPv4 datagram format IPv4 addressing ICMP IPv6
routing algorithms
Link state Distance Vector Hierarchical routing
routing in the Internet
RIP OSPF BGP
broadcast and multicast
routing
26/4-07 Datakommunikation - Jonny Pettersson, UmU
The Data Link Layer
Our goals:
understand principles
behind data link layer services:
error detection,
correction
sharing a broadcast
channel: multiple access
link layer addressing reliable data transfer,
flow control: done! instantiation and
implementation of various link layer technologies
Today
link layer services error detection, correction multiple access protocols and
LANs
link layer addressing, ARP,
DHCP
Next time
Ethernet hubs and switches PPP