1
Local Area Networks and Medium Access Control Protocols Multiple Access Networks
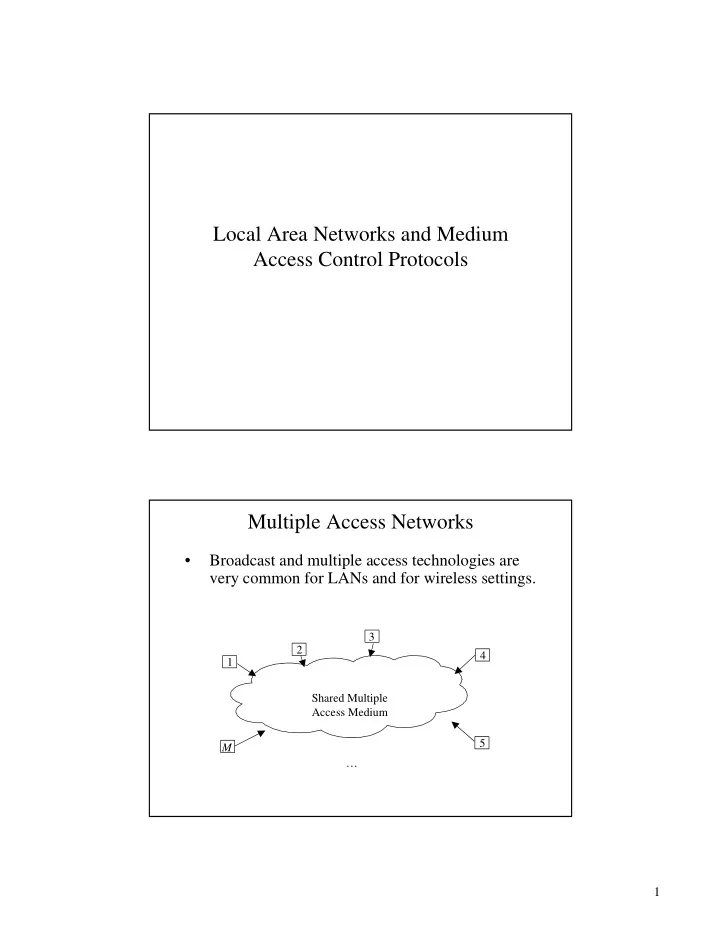
- Broadcast and multiple access technologies are
Local Area Networks and Medium Access Control Protocols Multiple - - PDF document
Local Area Networks and Medium Access Control Protocols Multiple Access Networks Broadcast and multiple access technologies are very common for LANs and for wireless settings. 3 2 4 1 Shared Multiple Access Medium 5 M 1
Aloha Slotted Aloha CSMA CSMA/CD
1,1 1,2 1,3 Station 1 2,1 2,2 Station 2 Station 3 3,1 3,2 Broadcast channel
Transmission Time (F) Complete Collision Partial Collision
frame
Vulnerable Period of red frame
F F
Frame which collides with start of red frame Frame which collides with end of red frame
1,1 1,2 1,3 Station 1 2,1 2,2 Station 2 Station 3 3,1 3,2 Broadcast channel
Transmission Time (F) Complete Collision Partial Collision
tG k
−
ALOHA Broadcast Channel ALOHA Broadcast Channel collisions S G Successful transmission New transmissions
G G
2 2
− −
G
2 −
1 max
−
G G
1 1
− −
G
−
1 max
−
0.05 0.1 0.15 0.2 0.25 0.3 0.35 0.4 0.01563 0.03125 0.0625 0.125 0.25 0.5 1 2 4 8
0.184 0.368
channel busy constant or variable delay ready Non-persistent: Transmit if idle;
1-persistent: Transmit as soon as channel goes idle. If collision, back off and try again p-persistent: Transmit as soon as channel goes idle, with probability
repeat process.
Figure 6.7
A transmits at t = 0
B transmits before t = tprop and detects collision shortly thereafter
A detects collision at t = 2 tprop
frame frame frame contention interval contention slot
1 1 1
− −
N N
1
−
N
1
−
j
j j
1 =
∞ = −
Network layer Network layer 802.2 Logical link layer Data link layer Physical layer 802.3 802.5 802.11 others Physical layer IEEE 802 OSI LLC MAC
transceiver
Ring interface To station From station
2 1 1
Illustration of Analysis (a > 1)
Illustration of Analysis (a < 1)
PHY coding/decoding transmit/receive data stream PHY coding/decoding transmit/receive data stream PMD conversion to optical signal PMD conversion to optical signal SMT initialization performance monitoring maintenance allocation of bandwidth configuration SMT initialization performance monitoring maintenance allocation of bandwidth configuration LLC(IEEE 802.2) Logical Link Control LLC(IEEE 802.2) Logical Link Control MAC ring access data transfer MAC ring access data transfer
SMT Station Management MAC Medium Access Control PHY Physical Layer Protocol PMD Physical Layer Medium Dependend
From Last Station To Next Station
To Concentrator
Preamble Preamble SD SD FC FC DA DA SA SA FCS FCS ED ED FS FS Info Info General Frame Format Preamble Preamble SD SD FC FC Token Frame Format
– 20 stations (single MAC) – 4km ring
– 100 stations (single MAC) – 200 km ring
– 500 stations (dual MAC) – 200 km ring
– 20 stations (single MAC) – 4km ring
– 100 stations (single MAC) – 200 km ring
– 500 stations (dual MAC) – 200 km ring