1
7/10 Link layer 1 Datakommunikation & Internet, Anders Broberg, UmU
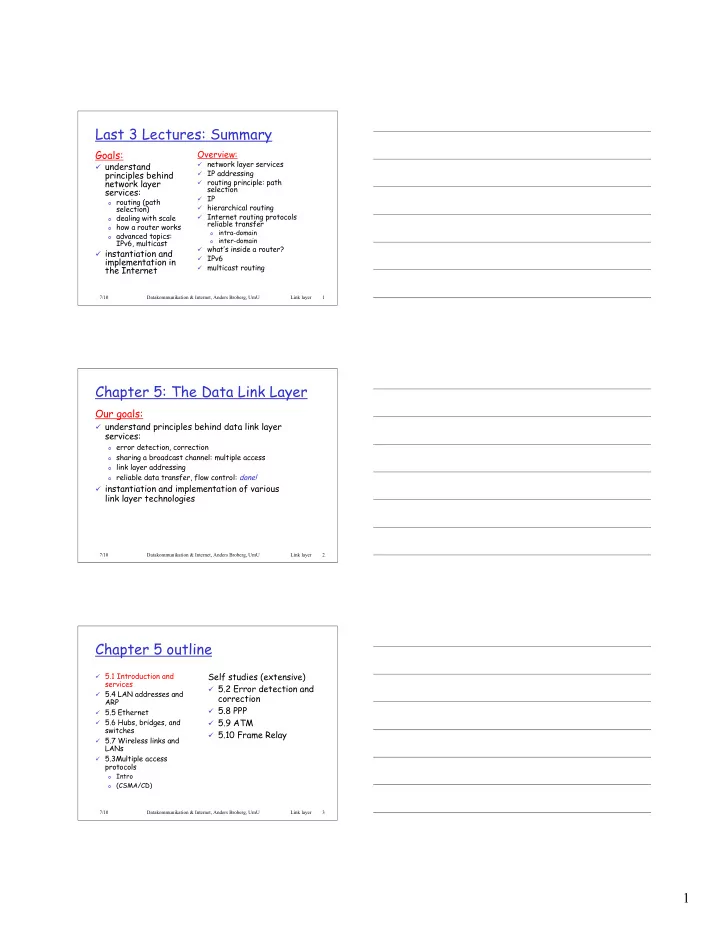
Last 3 Lectures: Summary
Goals:
understand
principles behind network layer services:
- routing (path
selection)
- dealing with scale
- how a router works
- advanced topics:
IPv6, multicast instantiation and
implementation in the Internet Overview:
network layer services IP addressing routing principle: path
selection
IP hierarchical routing Internet routing protocols
reliable transfer
- intra-domain
- inter-domain
what’s inside a router? IPv6 multicast routing
7/10 Link layer 2 Datakommunikation & Internet, Anders Broberg, UmU
Chapter 5: The Data Link Layer
Our goals:
understand principles behind data link layer
services:
- error detection, correction
- sharing a broadcast channel: multiple access
- link layer addressing
- reliable data transfer, flow control: done!
instantiation and implementation of various
link layer technologies
7/10 Link layer 3 Datakommunikation & Internet, Anders Broberg, UmU
Chapter 5 outline
5.1 Introduction and
services
5.4 LAN addresses and
ARP
5.5 Ethernet 5.6 Hubs, bridges, and
switches
5.7 Wireless links and
LANs
5.3Multiple access
protocols
- Intro
- (CSMA/CD)