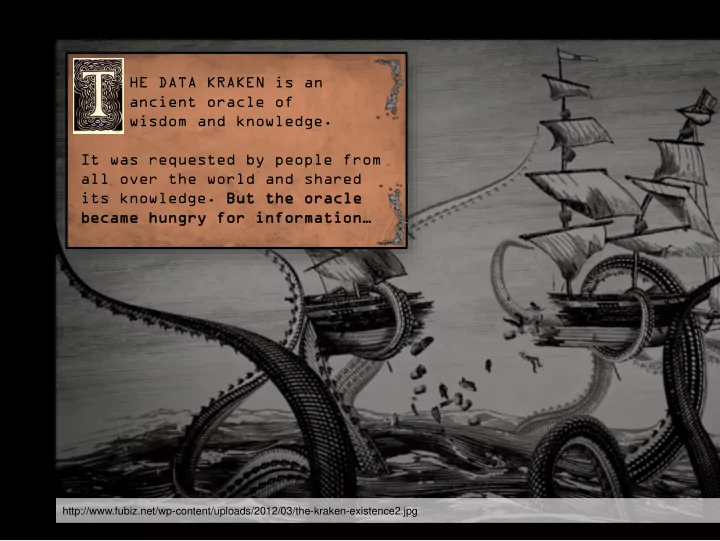
SLIDE 1 HE DATA KRAKEN is an ancient oracle of wisdom and knowledge. It was requested by people from all over the world and shared its knowledge. Bu But t th the e or
acle le became hungry for information…
http://www.fubiz.net/wp-content/uploads/2012/03/the-kraken-existence2.jpg

SLIDE 2
The Katzenpost Mix Network System
David Stainton
This project has received funding from the European Union’s Horizon 2020 research and innovation programme under the Grant Agreement No 653497, Privacy and Accountability in Networks via Optimized Randomized Mix-nets (Panoramix)”.

SLIDE 3
“we kill people based on metadata” –Michael Hayden (Ex-NSA and Ex-CIA Director)

SLIDE 4
David Chaum. Untraceable electronic mail, return addresses, and digital pseudonyms, Comm. ACM, 24, 2 (Feb. 1981)

SLIDE 5

SLIDE 6

SLIDE 7

SLIDE 8

SLIDE 9

SLIDE 10

SLIDE 11
See: Claudia Diaz & Andrei Serjantov. Generalising Mixes. PETS 2003

SLIDE 12

SLIDE 13

SLIDE 14

SLIDE 15
n-1 Attacks
From a Trickle to a Flood: Active Attacks on Several Mix Types by Andrei Serjantov and Roger Dingledine and, Paul Syverson

SLIDE 16
Ania Piotrowska, Jamie Hayes, Tariq Elahi, Sebastian Meiser, and George Danezis. The Loopix Anonymity System Usenix 26, 2017.

SLIDE 17
λM

SLIDE 18
Heartbeat Traffic to Counter (n-1) Attacks by George Danezis and Len Sassaman λM

SLIDE 19

SLIDE 20

SLIDE 21

SLIDE 22
Impact of Network Topology on Anonymity and Overhead in Low-Latency Anonymity Networks by Claudia Diaz, Stephen Murdoch and, Carmela Troncoso PETS 2010

SLIDE 23

SLIDE 24

SLIDE 25
Epistemic Attacks
Route Fingerprinting in Anonymous Communications by George Danezis and Richard Clayton

SLIDE 26

SLIDE 27

SLIDE 28

SLIDE 29

SLIDE 30

SLIDE 31

SLIDE 32

SLIDE 33
Statistical Disclosure Attacks
Statistical Disclosure or Intersection Attacks on Anonymity Systems by George Danezis and Andrei Serjantov Attacks do not always converge on success; depends on how repetitive and predictable client behavior is.

SLIDE 34
Sphinx: A Compact and Provably Secure Mix Format by George Danezis and Ian Goldberg IEEE Security and Privacy 2009

SLIDE 35

SLIDE 36

SLIDE 37

SLIDE 38
Compulsion Attacks
◮ legal action ◮ police raid ◮ pwn

SLIDE 39
Compulsion Attacks Defenses via Mix Key Erasure
“Forward Secure Mixes” by George Danezis, Proceedings of 7th Nordic Workshop on Secure IT Systems, 2002 “Xolotl: A request-and-forward mixnet format with selective statefulness for forward secure and hybrid post-quantum anonymity” by Jeffrey Burdges and Christian Grothoff

SLIDE 40
Other Defenses for Compulsion Attacks
”Compulsion Resistant Anonymous Communications” by George Danezis and Jolyon Clulow, Proceedings of Information Hiding Workshop, June 2005

SLIDE 41
“No right to ramain silent: Isolating Malicious Mixes” by Hemi Leibowitz, Ania Piotrowska, George Danezis and Amir Herzberg “Two Cents for Strong Anonymity: The Anonymous Post-office Protocol” by Nethanel Gelernter, Amir Herzberg, and Hemi Leibowitz

SLIDE 42

SLIDE 43

SLIDE 44

SLIDE 45
“Anonymity Trilemma” by Das, Meiser, Mohammadi, Kate (2017) Anonymity cannot scale better than |cover traffic| · |latency| Take aways: Tor’s situation: |cover traffic| ∗ 0 = 0

SLIDE 46
λP λL λD

SLIDE 47
λD

SLIDE 48
λL

SLIDE 49
λL

SLIDE 50
λP

SLIDE 51

SLIDE 52

SLIDE 53

SLIDE 54

SLIDE 55

SLIDE 56
The Katzenpost Free Software Project
Website: https://katzenpost.mixnetworks.org/ Github: https://github.com/katzenpost/ IRC: #katzenpost on OFTC Contact me:
◮ E-mail: dawuud@riseup.net ◮ Twitter: @david415