Greatest Common Divisor
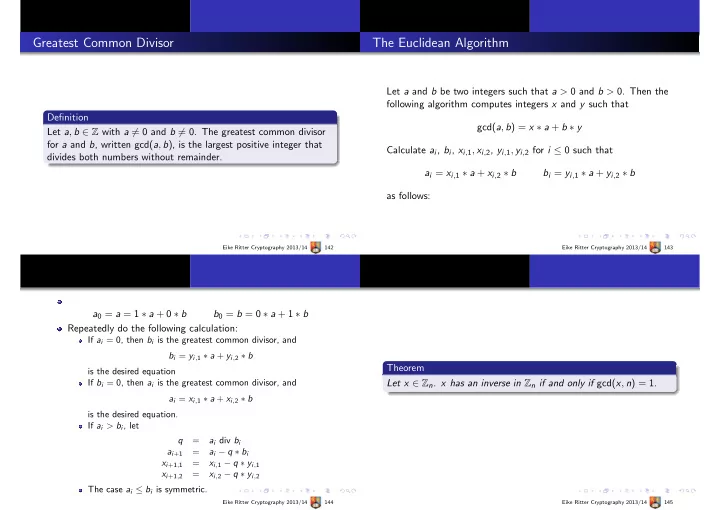
Definition Let a, b ∈ Z with a = 0 and b = 0. The greatest common divisor for a and b, written gcd(a, b), is the largest positive integer that divides both numbers without remainder.
Eike Ritter Cryptography 2013/14 142
The Euclidean Algorithm
Let a and b be two integers such that a > 0 and b > 0. Then the following algorithm computes integers x and y such that gcd(a, b) = x ∗ a + b ∗ y Calculate ai, bi, xi,1, xi,2, yi,1, yi,2 for i ≤ 0 such that ai = xi,1 ∗ a + xi,2 ∗ b bi = yi,1 ∗ a + yi,2 ∗ b as follows:
Eike Ritter Cryptography 2013/14 143
a0 = a = 1 ∗ a + 0 ∗ b b0 = b = 0 ∗ a + 1 ∗ b Repeatedly do the following calculation:
If ai = 0, then bi is the greatest common divisor, and bi = yi,1 ∗ a + yi,2 ∗ b is the desired equation If bi = 0, then ai is the greatest common divisor, and ai = xi,1 ∗ a + xi,2 ∗ b is the desired equation. If ai > bi, let q = ai div bi ai+1 = ai − q ∗ bi xi+1,1 = xi,1 − q ∗ yi,1 xi+1,2 = xi,2 − q ∗ yi,2 The case ai ≤ bi is symmetric.
Eike Ritter Cryptography 2013/14 144
Theorem Let x ∈ Zn. x has an inverse in Zn if and only if gcd(x, n) = 1.
Eike Ritter Cryptography 2013/14 145