1
Page 1 Page 1
Mutual Exclusion & Election Algoritms
Paul Krzyzanowski pxk@cs.rutgers.edu
Distributed Systems
Except as otherwise noted, the content of this presentation is licensed under the Creative Commons Attribution 2.5 License.
Page 2 Page 2
Mutual Exclusion & Election Algorithms
Page 3
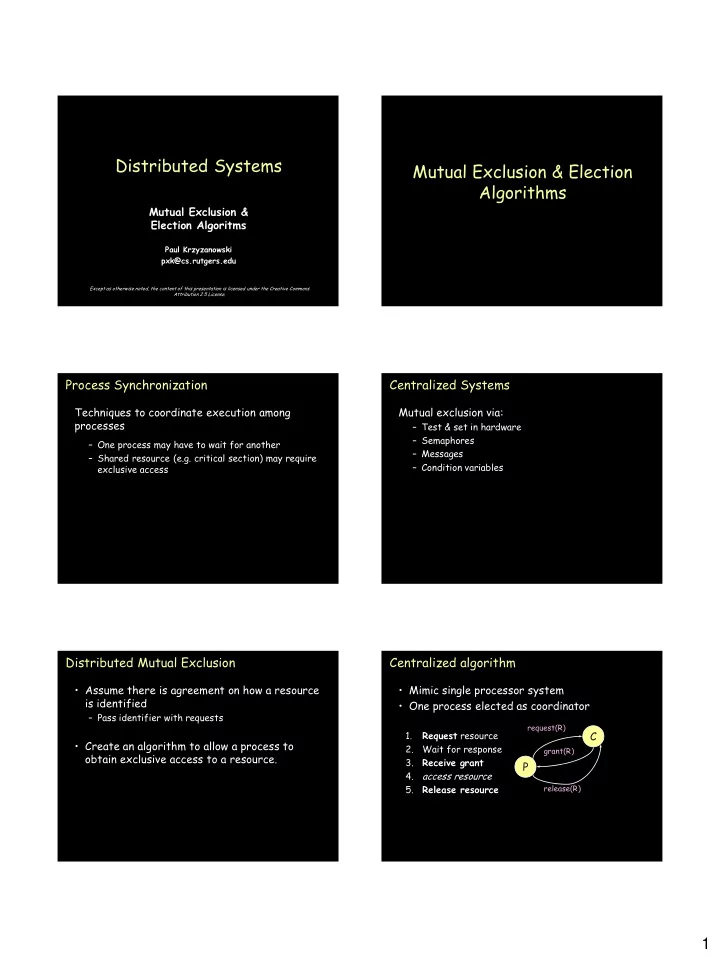
Process Synchronization
Techniques to coordinate execution among processes
– One process may have to wait for another – Shared resource (e.g. critical section) may require exclusive access
Page 4
Centralized Systems
Mutual exclusion via:
– Test & set in hardware – Semaphores – Messages – Condition variables
Page 5
Distributed Mutual Exclusion
- Assume there is agreement on how a resource
is identified
– Pass identifier with requests
- Create an algorithm to allow a process to
- btain exclusive access to a resource.
Page 6
Centralized algorithm
- Mimic single processor system
- One process elected as coordinator
P C
request(R) grant(R)
1. Request resource 2. Wait for response 3. Receive grant 4. access resource 5. Release resource
release(R)