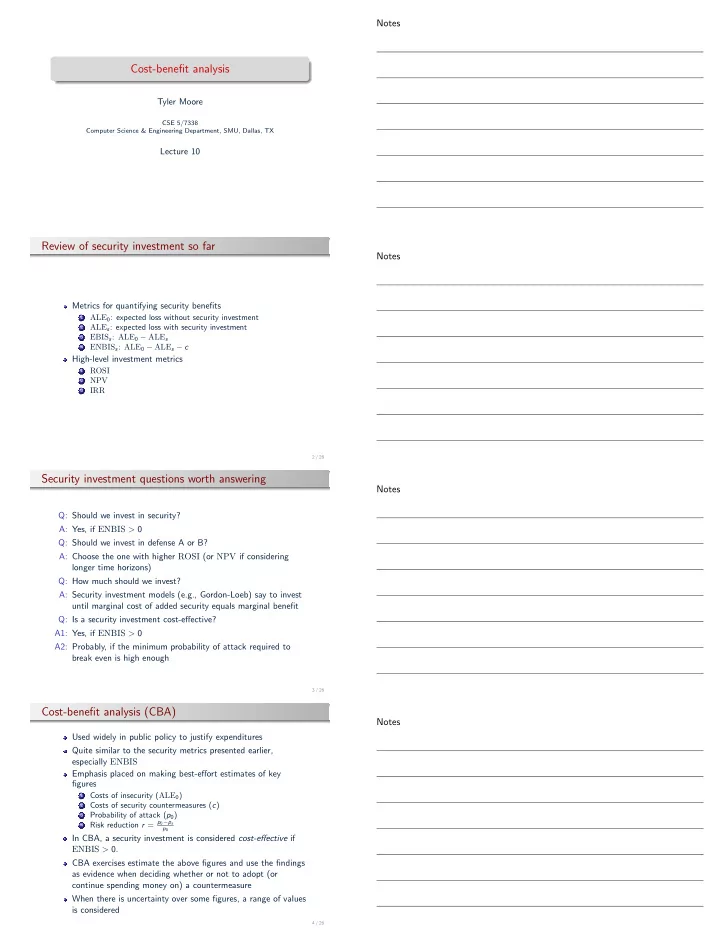
Cost-benefit analysis
Tyler Moore
CSE 5/7338 Computer Science & Engineering Department, SMU, Dallas, TX
Lecture 10
Review of security investment so far
Metrics for quantifying security benefits
1
ALE0: expected loss without security investment
2
ALEs: expected loss with security investment
3
EBISs: ALE0 − ALEs
4
ENBISs: ALE0 − ALEs − c
High-level investment metrics
1
ROSI
2
NPV
3
IRR
2 / 26
Security investment questions worth answering
Q: Should we invest in security? A: Yes, if ENBIS > 0 Q: Should we invest in defense A or B? A: Choose the one with higher ROSI (or NPV if considering longer time horizons) Q: How much should we invest? A: Security investment models (e.g., Gordon-Loeb) say to invest until marginal cost of added security equals marginal benefit Q: Is a security investment cost-effective? A1: Yes, if ENBIS > 0 A2: Probably, if the minimum probability of attack required to break even is high enough
3 / 26
Cost-benefit analysis (CBA)
Used widely in public policy to justify expenditures Quite similar to the security metrics presented earlier, especially ENBIS Emphasis placed on making best-effort estimates of key figures
1
Costs of insecurity (ALE0)
2
Costs of security countermeasures (c)
3
Probability of attack (p0)
4
Risk reduction r = p0−ps
p0
In CBA, a security investment is considered cost-effective if ENBIS > 0. CBA exercises estimate the above figures and use the findings as evidence when deciding whether or not to adopt (or continue spending money on) a countermeasure When there is uncertainty over some figures, a range of values is considered
4 / 26