Optimal filter and Cost-Benefit Analysis
Tyler Moore
CSE 7338 Computer Science & Engineering Department, SMU, Dallas, TX
Lecture 3
Outline
1
Information security risk management
2
Optimal filter configuration
3
Cost-benefit analysis
2 / 53 Information security risk management
Information security risk management
Just as it can be useful to translate infosec risks and defenses into the language of investment (ROSI, NPV, etc.), one must also be aware of terminology from risk management As IT becomes essential to many businesses, border between information security investment and general risk management has blurred
4 / 53 Information security risk management
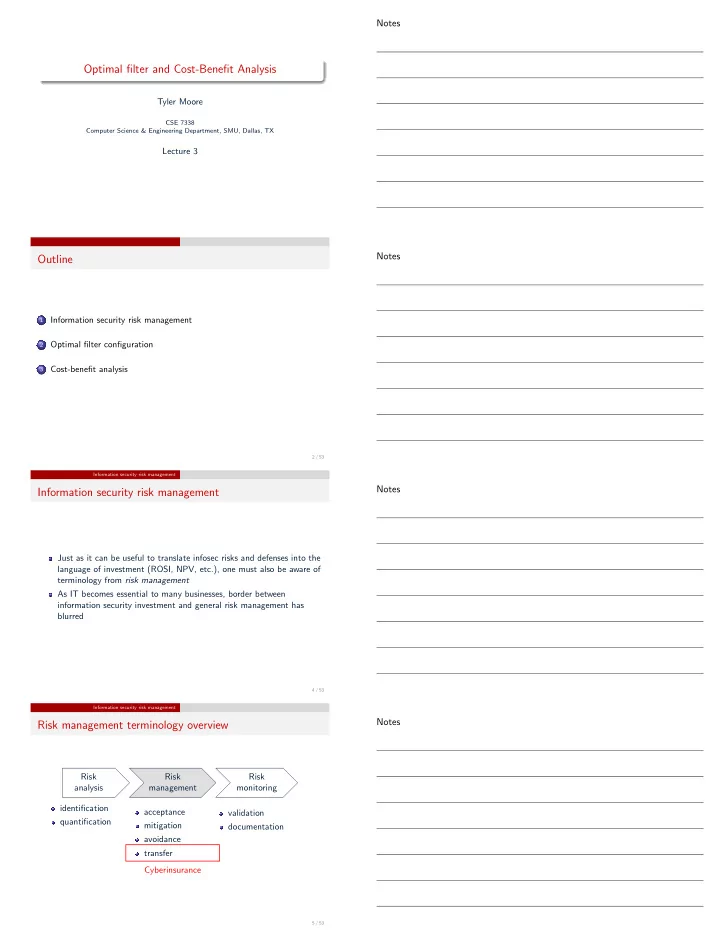
Risk management terminology overview
Risk analysis identification quantification Risk management acceptance mitigation avoidance transfer Risk monitoring validation documentation Cyberinsurance
5 / 53