1
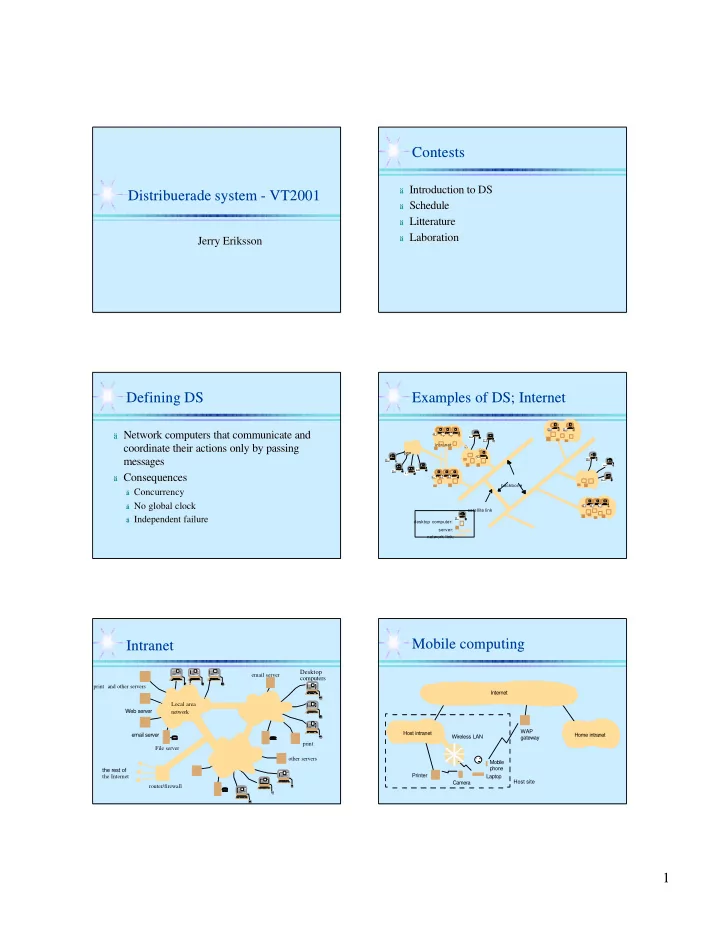
Distribuerade system - VT2001 Distribuerade system - VT2001
Jerry Eriksson Jerry Eriksson
Contests Contests
ä Introduction to DS
Introduction to DS
ä Schedule
Schedule
ä Litterature
Litterature
ä Laboration
Laboration
Defining DS Defining DS
ä Network computers that communicate and
Network computers that communicate and coordinate their actions only by passing coordinate their actions only by passing messages messages
ä Consequences
Consequences
ä Concurrency
Concurrency
ä No global clock
No global clock
ä Independent failure
Independent failure
Examples of DS; Internet Examples of DS; Internet
intranet ISP desktop computer: backbone satellite link server:
- network link:
- Intranet
Intranet
the rest of email server Web server
Desktop computers
File server router/firewall print and other servers
- ther servers
print Local area network email server the Internet
Mobile computing Mobile computing
Laptop Mobile Printer Camera Internet Host intranet Home intranet WAP Wireless LAN phone gateway Host site