Special Course on Networked Virtual Environments January 29, 2004 Jouni Smed 1
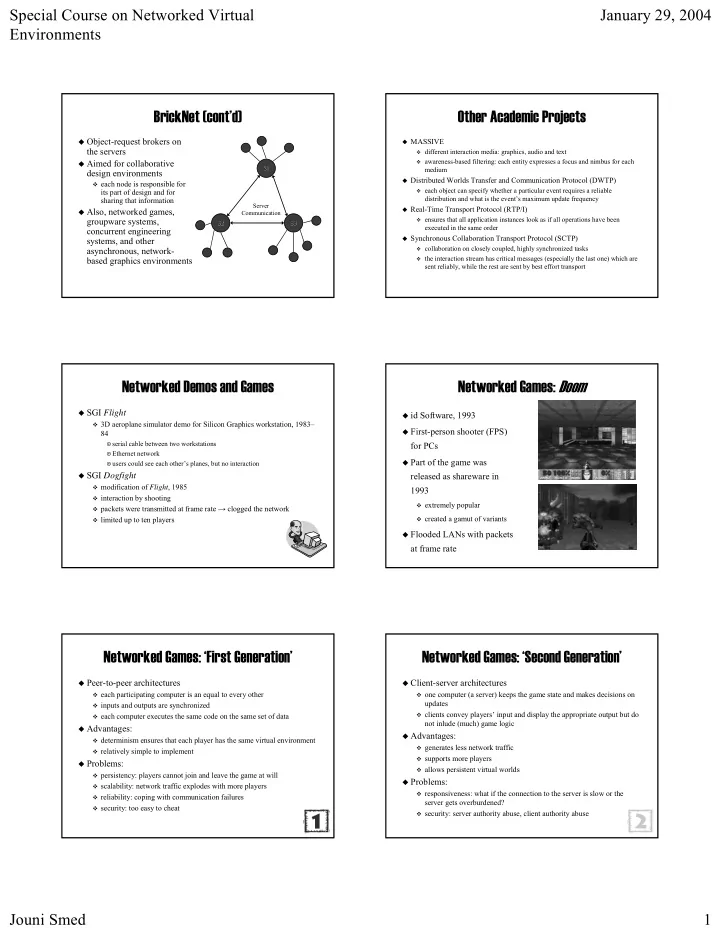
BrickNet BrickNet (cont’d) (cont’d)
- Object
Object-
- request brokers on
request brokers on the servers the servers
- Aimed for collaborative
Aimed for collaborative design environments design environments
- each node is responsible for
each node is responsible for its part of design and for its part of design and for sharing that information sharing that information
- Also, networked games,
Also, networked games, groupware groupware systems, systems, concurrent engineering concurrent engineering systems, and other systems, and other asynchronous, network asynchronous, network-
- based graphics environments
based graphics environments
S1 S1 S3 S3 S2 S2 Server Server Communication Communication
Other Academic Projects Other Academic Projects
- MASSIVE
MASSIVE
- different interaction media: graphics, audio and text
different interaction media: graphics, audio and text
- awareness
awareness-
- based filtering: each entity expresses a focus and nimbus for ea
based filtering: each entity expresses a focus and nimbus for each ch medium medium
- Distributed Worlds Transfer and Communication Protocol (DWTP)
Distributed Worlds Transfer and Communication Protocol (DWTP)
- each object can specify whether a particular event requires a re
each object can specify whether a particular event requires a reliable liable distribution and what is the event’s maximum update frequency distribution and what is the event’s maximum update frequency
- Real
Real-
- Time Transport Protocol (RTP/I)
Time Transport Protocol (RTP/I)
- ensures that all application instances look as if all operations
ensures that all application instances look as if all operations have been have been executed in the same order executed in the same order
- Synchronous Collaboration Transport Protocol (SCTP)
Synchronous Collaboration Transport Protocol (SCTP)
- collaboration on closely coupled, highly synchronized tasks
collaboration on closely coupled, highly synchronized tasks
- the interaction stream has critical messages (especially the las
the interaction stream has critical messages (especially the last one) which are t one) which are sent reliably, while the rest are sent by best effort transport sent reliably, while the rest are sent by best effort transport
Networked Demos and Games Networked Demos and Games
- SGI
SGI Flight Flight
- 3D aeroplane simulator demo
3D aeroplane simulator demo for Silicon for Silicon Graphics workstation, Graphics workstation, 1983 1983– – 84 84
- serial
serial cable between two workstations cable between two workstations
- Ethernet network
Ethernet network
- users could see each other’s planes, but no
users could see each other’s planes, but no interaction interaction
- SGI
SGI Dogfight Dogfight
- modification of
modification of Flight Flight, 1985 , 1985
- interaction by shooting
interaction by shooting
- packets were transmitted at frame
packets were transmitted at frame rate → clogged rate → clogged the network the network
- limited up
limited up to ten players to ten players
Networked Networked Games: Games: Doom Doom
- id Software, 1993
id Software, 1993
- First
First-
- person
person shooter shooter (FPS) (FPS) for PCs for PCs
- Part of the game was
Part of the game was released as shareware released as shareware in in 1993 1993
- extremely popular
extremely popular
- created a gamut of variants
created a gamut of variants
- Flooded LANs with packets
Flooded LANs with packets at frame rate at frame rate
Networked Games: ‘First Generation’ Networked Games: ‘First Generation’
- Peer
Peer-
- to
to-
- peer architectures
peer architectures
- each participating computer is an equal to every other
each participating computer is an equal to every other
- inputs and outputs are synchronized
inputs and outputs are synchronized
- each computer executes the same code on the same set of data
each computer executes the same code on the same set of data
- Advantages:
Advantages:
- determinism ensures that each player has the same virtual enviro
determinism ensures that each player has the same virtual environment nment
- relatively simple to implement
relatively simple to implement
- Problems:
Problems:
- persistency: players cannot join and leave the game at will
persistency: players cannot join and leave the game at will
- scalability: network traffic explodes with more players
scalability: network traffic explodes with more players
- reliability: coping with communication failures
reliability: coping with communication failures
- security: too easy to cheat
security: too easy to cheat
Networked Games: ‘Second Generation’ Networked Games: ‘Second Generation’
- Client
Client-
- server architectures
server architectures
- ne computer (a server) keeps the game state and makes decisions
- ne computer (a server) keeps the game state and makes decisions on
- n
updates updates
- clients convey players’ input and display the appropriate output
clients convey players’ input and display the appropriate output but do but do not inlude (much) game logic not inlude (much) game logic
- Advantages:
Advantages:
- generates less network traffic
generates less network traffic
- supports more players
supports more players
- allows persistent virtual worlds
allows persistent virtual worlds
- Problems:
Problems:
- responsiveness: what if the connection to the server is slow or
responsiveness: what if the connection to the server is slow or the the server gets overburdened? server gets overburdened?
- security: server authority abuse, client authority abuse
security: server authority abuse, client authority abuse