Application Centric Infrastructure (ACI)
The Cisco Application Centric Infrastructure (ACI) allows application requirements to dene the network. This architecture simplies, optimizes, and accelerates the entire application deployment life cycle.
Application Policy Infrastructure Controller (APIC)
The APIC manages the scalable ACI multi-tenant fabric. The APIC provides a unied point of automation and management, policy programming, application deployment, and health monitoring for the fabric. The APIC, which is implemented as a replicated synchronized clustered controller, optimizes performance, supports any application anywhere, and provides unied operation of the physical and virtual infrastructure. The APIC enables network administrators to easily dene the
- ptimal network for applications. Data center operators can clearly see how applications consume network resources, easily
isolate and troubleshoot application and infrastructure problems, and monitor and prole resource usage patterns. The Cisco Application Policy Infrastructure Controller (APIC) API enables applications to directly connect with a secure, shared, high-performance resource pool that includes network, compute, and storage capabilities.
Cisco ACI Provider
The Cisco ACI terraform provider is used to interact with resources provided by Cisco APIC. The provider needs to be congured with proper credentials to authenticate with Cisco APIC.
Authentication
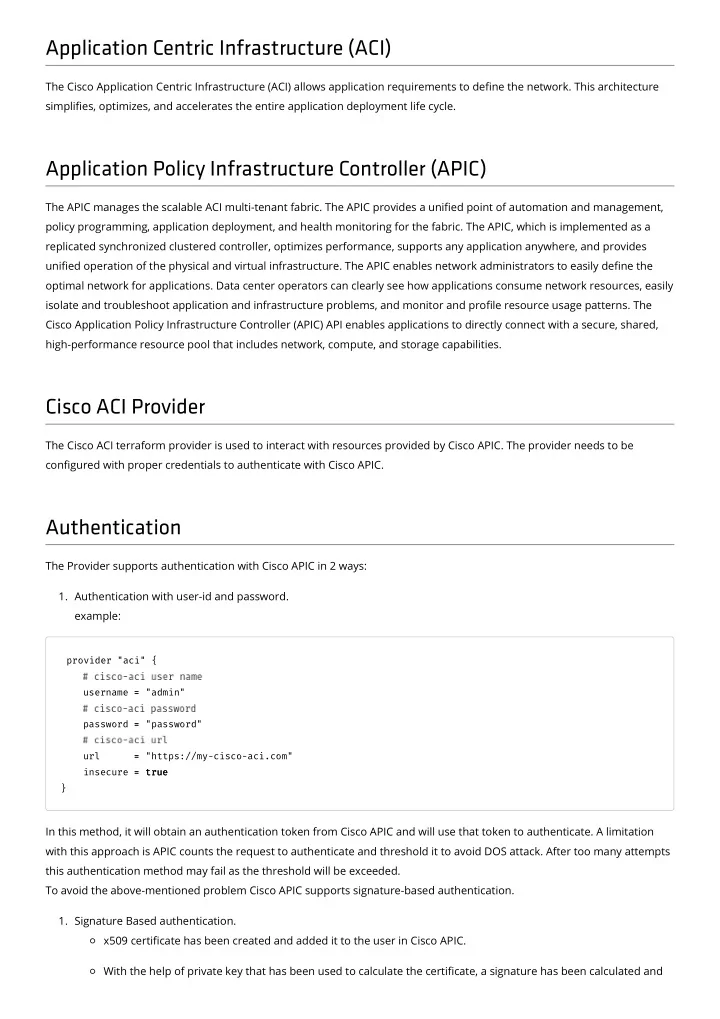
The Provider supports authentication with Cisco APIC in 2 ways:
- 1. Authentication with user-id and password.
example:
provider "aci" { username = = "admin" password = = "password" url = = "https://my-cisco-aci.com" insecure = = true true }
In this method, it will obtain an authentication token from Cisco APIC and will use that token to authenticate. A limitation with this approach is APIC counts the request to authenticate and threshold it to avoid DOS attack. After too many attempts this authentication method may fail as the threshold will be exceeded. To avoid the above-mentioned problem Cisco APIC supports signature-based authentication.
- 1. Signature Based authentication.
x509 certicate has been created and added it to the user in Cisco APIC. With the help of private key that has been used to calculate the certicate, a signature has been calculated and