1
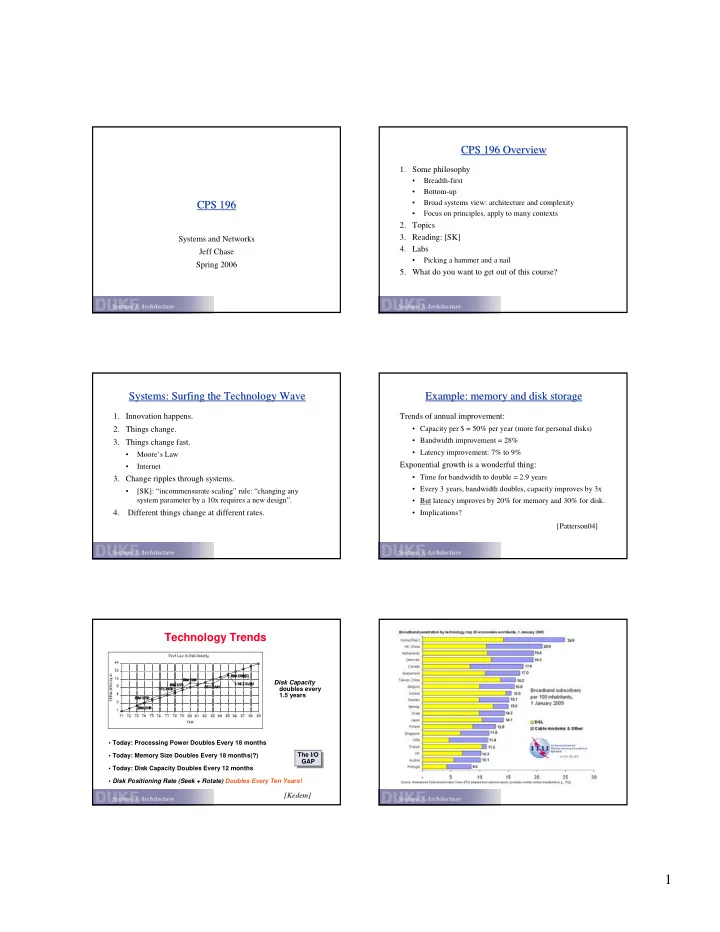
CPS 196 CPS 196
Systems and Networks Jeff Chase Spring 2006
CPS 196 Overview CPS 196 Overview
- 1. Some philosophy
- Breadth-first
- Bottom-up
- Broad systems view: architecture and complexity
- Focus on principles, apply to many contexts
- 2. Topics
- 3. Reading: [SK]
- 4. Labs
- Picking a hammer and a nail
- 5. What do you want to get out of this course?
Systems: Surfing the Technology Wave Systems: Surfing the Technology Wave
- 1. Innovation happens.
- 2. Things change.
- 3. Things change fast.
- Moore’s Law
- Internet
- 3. Change ripples through systems.
- [SK]: “incommensurate scaling” rule: “changing any
system parameter by a 10x requires a new design”.
- 4. Different things change at different rates.
Example: memory and disk storage Example: memory and disk storage
Trends of annual improvement:
- Capacity per $ = 50% per year (more for personal disks)
- Bandwidth improvement = 28%
- Latency improvement: 7% to 9%
Exponential growth is a wonderful thing:
- Time for bandwidth to double = 2.9 years
- Every 3 years, bandwidth doubles, capacity improves by 3x
- But latency improves by 20% for memory and 30% for disk.
- Implications?
[Patterson04]
Technology Trends
Disk Capacity doubles every 1.5 years
- Today: Processing Power Doubles Every 18 months
- Today: Memory Size Doubles Every 18 months(?)
- Today: Disk Capacity Doubles Every 12 months
- Disk Positioning Rate (Seek + Rotate) Doubles Every Ten Years!
The I/O GAP The I/O GAP
[Kedem]