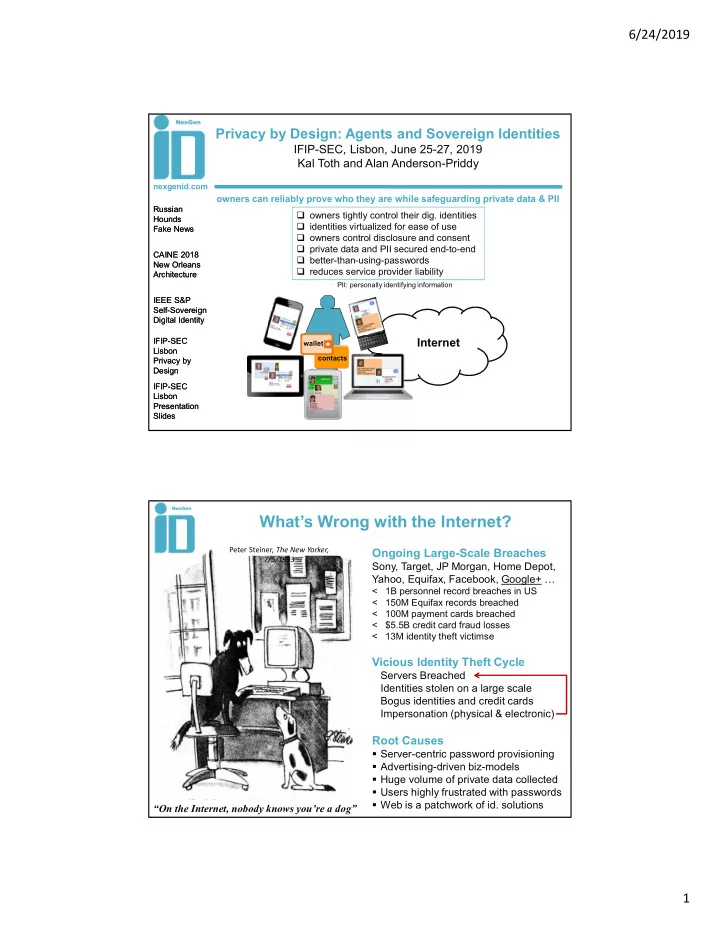
6/24/2019 1 Privacy by Design: Agents and Sovereign Identities
IFIP-SEC, Lisbon, June 25-27, 2019 Kal Toth and Alan Anderson-Priddy
owners tightly control their dig. identities identities virtualized for ease of use owners control disclosure and consent private data and PII secured end-to-end better-than-using-passwords reduces service provider liability
nexgenid.com Russian Hounds Fake News Russian Hounds Fake News CAINE 2018 New Orleans Architecture CAINE 2018 New Orleans Architecture IEEE S&P Self-Sovereign Digital Identity IEEE S&P Self-Sovereign Digital Identity IFIP-SEC Lisbon Privacy by Design IFIP-SEC Lisbon Privacy by Design IFIP-SEC Lisbon Presentation Slides IFIP-SEC Lisbon Presentation Slides
- wners can reliably prove who they are while safeguarding private data & PII
PII: personally identifying information
Internet
contacts wallet
Peter Steiner, The New Yorker, 7/5/1993
“On the Internet, nobody knows you’re a dog”
Ongoing Large-Scale Breaches
Sony, Target, JP Morgan, Home Depot, Yahoo, Equifax, Facebook, Google+ …
< 1B personnel record breaches in US < 150M Equifax records breached < 100M payment cards breached < $5.5B credit card fraud losses < 13M identity theft victimse
What’s Wrong with the Internet?
Root Causes
- Server-centric password provisioning
- Advertising-driven biz-models
- Huge volume of private data collected
- Users highly frustrated with passwords
- Web is a patchwork of id. solutions