29 March, 2002 1
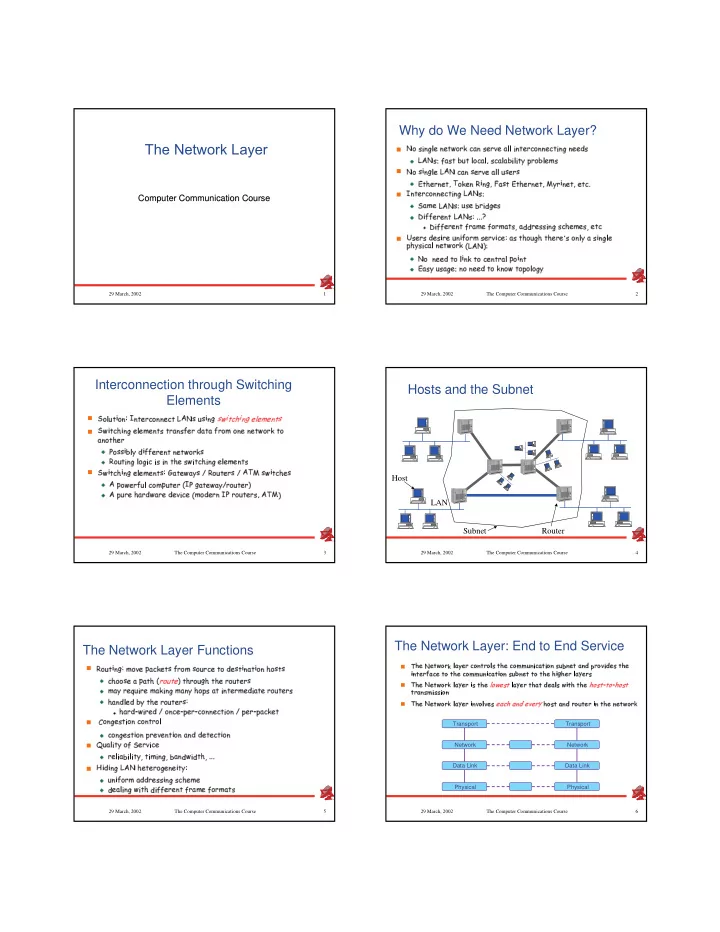
The Network Layer
Computer Communication Course Computer Communication Course
2 29 March, 2002 The Computer Communications Course
Why do We Need Network Layer?
- ✁✄✂✆☎✞✝
- ✁✄✂✆☎✞✝
- ✾☞✟✡✏
- ❄❅☎✡✌✚✓
3 29 March, 2002 The Computer Communications Course
Interconnection through Switching Elements
- ✿✒✂☞☛
- ☞❍✒■
- ✿❅✑★✝
- ✿❅✑★✝
4 29 March, 2002 The Computer Communications Course
Hosts and the Subnet
Subnet Router LAN Host
5 29 March, 2002 The Computer Communications Course
The Network Layer Functions
- ✺☞✂✤✭✕✏✢✝
- ❭✚✂✚✟✡✠✢✌✤☎✕✏✢✝
- ❪✱✭✕✘✚☛
- ❫✬✝
6 29 March, 2002 The Computer Communications Course
The Network Layer: End to End Service
Transport Network Data Link Physical Transport Network Data Link Physical
❴ ❵✲❛✡❜✬❝❞❜✡❡ ❢☞❣✕❤ ✐✙❥ ❦ ❧✡❜✢❤❞♠ ❣✕♥ ❡✎❤ ❣✢❥ ♦❅❡ ❛✕❜✬♠ ❣✢♣❞♣❅q✎♥✕r ♠ ❦ ❡✡r ❣✕♥★♦ q✡s✢♥ ❜✡❡❞❦✡♥✎t✬✉✕❤ ❣✕✈✎r t✕❜✢♦❅❡ ❛✕❜ r ♥ ❡ ❜✢❤ ✇ ❦✕♠ ❜✄❡ ❣★❡ ❛✕❜✬♠ ❣✕♣❞♣❅q✡♥✕r ♠ ❦✎❡✡r ❣✕♥★♦ q✡s✢♥ ❜✡❡❞❡ ❣★❡ ❛✕❜✙❛✞r ①✕❛✕❜✢❤❁❥ ❦ ❧✡❜✢❤ ♦ ❴ ❵✲❛✡❜✬❝❞❜✡❡ ❢☞❣✕❤ ✐✙❥ ❦ ❧✡❜✢❤❁r ♦❞❡ ❛✡❜ ② ③✢④✤⑤✕⑥✢⑦ ❥ ❦ ❧✡❜✢❤✒❡ ❛✕❦✎❡❞t✢❜✡❦✢❥ ♦❞❢✒r ❡ ❛✄❡ ❛✕❜ ⑧✢③ ⑥✤⑦ ⑨ ⑦ ③✕⑨ ⑧✕③✎⑥✢⑦ ❡✎❤ ❦✡♥✎♦✎♣❁r ♦ ♦✡r ❣✕♥ ❴ ❵✲❛✡❜✬❝❞❜✡❡ ❢☞❣✕❤ ✐✙❥ ❦ ❧✡❜✢❤❁r ♥✎✈ ❣✢❥ ✈ ❜✕♦ ⑤✢⑩✡❶ ⑧✬⑩ ❷✕❸✄⑤✹❹ ⑤✢❺ ❻ ❛✡❣✕♦ ❡❞❦✡♥✎t✗❤ ❣✡q ❡ ❜✤❤❁r ♥❁❡ ❛✕❜✙♥✎❜✡❡ ❢☞❣✕❤ ✐