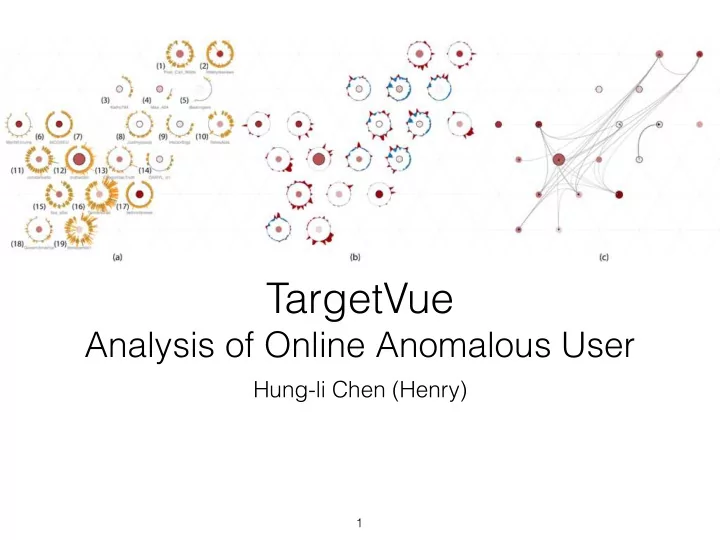
TargetVue
Analysis of Online Anomalous User
Hung-li Chen (Henry)
1
TargetVue Analysis of Online Anomalous User Hung-li Chen (Henry) - - PowerPoint PPT Presentation
TargetVue Analysis of Online Anomalous User Hung-li Chen (Henry) 1 Target Vue: Visual Analysis of Anomalous User Behaviours in Online Communication Systems (TVCG, 2016) Nan Cao, Conglei Shi, Sabrina Lin, Jie Lu, Yu-Ru Lin, Ching-Yung
Hung-li Chen (Henry)
1
Nan Cao, Conglei Shi, Sabrina Lin, Jie Lu, Yu-Ru Lin, Ching-Yung Lin First five authors are from IBM T.J. Watson Research Centre The last author is from University of Pittsburgh not Pissburg…
2
3
4
Context
Contribution
interactive exploration of anomalous users
case a case study
5
6
Network, User Profile
7
8
perspectives
9
10
11
Time Adaptive Local Outlier Factor Choosing Features
12
Global View User List Messages Inspection Feature Variation Propagation
13
kernel density estimation
14
information, raw messages
tag cloud, list of messages and user profiles
and overview
15
baseline), users in communication threads
(introduced in FluxFlow)
16
number of users involved, sentiment of the threads
color (sentiment), intersection (time when the user join).
17
18
19
neighbouring glyphs
20
21
Query Box Filter (range slider) Highlight Select for Inspection Context Switch Zoom and Pan Data Labeling
22
challenge.
powerful”
23
requirements and tasks).
identifying anomalies, encoding may not be the most visually effective.
built on hadoop, used the system for twitter data of 8000 users and 4M tweets)
24
25