SLIDE 1 RSA Example
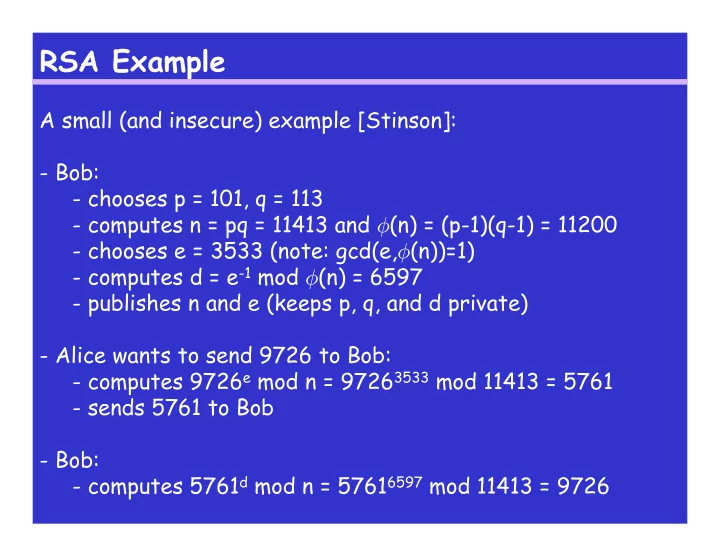
A small (and insecure) example [Stinson]:
- Bob:
- chooses p = 101, q = 113
- computes n = pq = 11413 and φ(n) = (p-1)(q-1) = 11200
- chooses e = 3533 (note: gcd(e,φ(n))=1)
- computes d = e-1 mod φ(n) = 6597
- publishes n and e (keeps p, q, and d private)
- Alice wants to send 9726 to Bob:
- computes 9726e mod n = 97263533 mod 11413 = 5761
- sends 5761 to Bob
- Bob:
- computes 5761d mod n = 57616597 mod 11413 = 9726

SLIDE 2 RSA Correctly Decrypts
Need to show that for any plaintext m ∈ Zn, (me)d mod n = m. We will need some number theory: If gcd(m,n)=1:
- we will use Euler’s Theorem (pg 81):
If gcd(a,n)=1, then aφ(n) ≡ 1 (mod n)
- can we conclude that (me)d mod n = m ?
If gcd(m,n)>1:
- we will use the Chinese Remainder Theorem (Section 3.4)

SLIDE 3
Chinese Remainder Theorem
Suppose m1,…,mk are pairwise relatively prime positive integers, and suppose a1,…,ak are integers. Then the system of congruences x ≡ ai (mod mi) (1 ≤ i ≤ k) has a unique solution modulo M = m1m2…mk, which is given by x = ∑i=1…k aiMiyi mod M, where Mi = M/mi and yi = Mi−1 mod mi, for 1 ≤ i ≤ k.

SLIDE 4
Chinese Remainder Theorem
Example: We want to find x that satisfies the following congruencies: x ≡ 5 (mod 7) x ≡ 3 (mod 11) x ≡ 10 (mod 13) The solutions is unique mod ____: x =

SLIDE 5
RSA Correctly Decrypts, part 2
If m is not divisible by p: If m is divisible by p:

SLIDE 6
RSA Correctly Decrypts, part 2
So, for all m: (me)d ≡ m (mod p). What can we conclude ?

SLIDE 7
RSA: Computational Issues
We showed that RSA works (i.e., correctly decrypts). But… Can we actually compute me mod n for very large numbers ?

SLIDE 8
RSA: Computational Issues
We showed that RSA works (i.e., correctly decrypts). But… Can we actually compute me mod n for very large numbers ?

SLIDE 9
RSA: Computational Issues
Want: algorithms polynomial in the length of n. What is the length of n ? Note: typically when estimating the running time of an algorithm, arithmetic operations are counted as taking constant time – but this is NOT feasible in cryptography where the numbers can be very large (recommended size of p,q in RSA: 1024 bits)

SLIDE 10 RSA: Computational Issues
Modular Arithmetic: Give upper bounds (using the big-Oh notation) on the running time of the following operations in Zn:
- addition
- difference
- multiplication
- exponentiation
- gcd
- inverse
- RSA encryption
- RSA decryption

SLIDE 11 RSA: Computational Issues
Modular Arithmetic: Give upper bounds (using the big-Oh notation) on the running time of the following operations in Zn:
- addition
- difference
- multiplication
- exponentiation
- gcd
- inverse
- RSA encryption
- RSA decryption