IP Traffic Engineering
by Sorin M. SCHWARTZ www.sorin-schwartz.com
- ver. 05-12-31
IP Traffic Engineering 1
ROUTING vs. FORWARDING www.sorin-schwartz.com ROUTERS EVOLUTION - - PowerPoint PPT Presentation
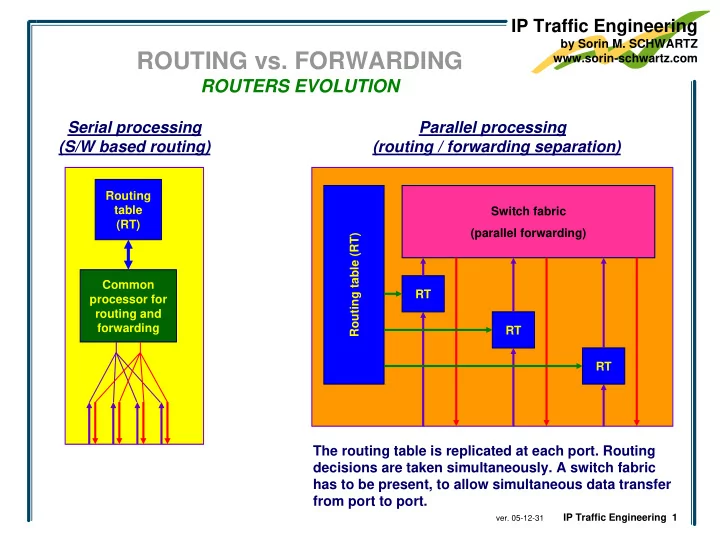
IP Traffic Engineering by Sorin M. SCHWARTZ ROUTING vs. FORWARDING www.sorin-schwartz.com ROUTERS EVOLUTION Serial processing Parallel processing (S/W based routing) (routing / forwarding separation) Routing table Switch fabric (RT)
IP Traffic Engineering 1
IP Traffic Engineering 2
RT RT RT Routing table (RT) Switch fabric (parallel forwarding) Routing table (RT) Switch fabric (parallel forwarding) Routing table (RT) Switch fabric (parallel forwarding) add LABEL remove LABEL
IP Traffic Engineering 3
LSR 3 LSR 4 LSR 7 LSR 1
LSR 5 1 2 3 1 2 LSR 6
IP DA = Y payload
L211
IP DA = Y payload
1 LSR 2 1 2 L652
IP DA = Y payload
L411
IP DA = T payload
L161
IP DA = payloa Y d
L363 L162
IP DA = T payload
L363 L672
IP DA = T payload
FEC NHLFE (Next Hop Label Forwarding Entry)
NHLFE (1) (2) next hop LSR5 LSR7
label swap label swap label L651 L671 physical interface 1 2
label NHLFE (Next Hop Label Forwarding Entry) 361 (1) 362 (2)
363 (3) (3)
L363
(4) (4) LSR5 label swap L652 1 162 (5) (5) LSR7 label swap L672 2
IP Traffic Engineering 4
DA
SA
Type = IP S LABEL EXP TTL DA
SA Type = MPLS
1
DA
SA
Type = ??
LSR 1 LSR 2
IP Traffic Engineering 5
site 2 site 4 site 1 site 3 site 5
site 6 site 7
VRF site 2 VRF site 4 BGP tables IGP and MPLS tables
VRF site 6 VRF site 7 BGP tables IGP and MPLS tables IGP and MPLS tables
IGP and MPLS tables IGP LDP IGP LDP IGP LDP
(simplified) MP-iBGP session
To destination net3 Deliver to router PE4 int’f FEC site6:net3 (L63)
To destination site6:net3 Deliver to router PE4 int’f FEC site6:net3 (L63)
To destination PE4 Deliver to router PE4 nr of hops physical interface FEC a / L15
IP Traffic Engineering 6
the travel through the network are set to “0” (e.g. time to live) variable length input data
Original packet before authentication process (IP header + payload)
Authentication Field
ICV Original packet (IP header + payload) hash function
encryption key MAC fixed length
(128 or 160 bits)
SHA-1 MD5 DES 3DES HMAC-SHA-1-96 HMAC-MD5-96 encryption function
Packet with added authentication fields , including ICV field (sent to the other site)