Trustworthy Cyber Infrastructure for the Power Grid
Presentations
1
University of Illinois Dartmouth College Cornell University Washington State University
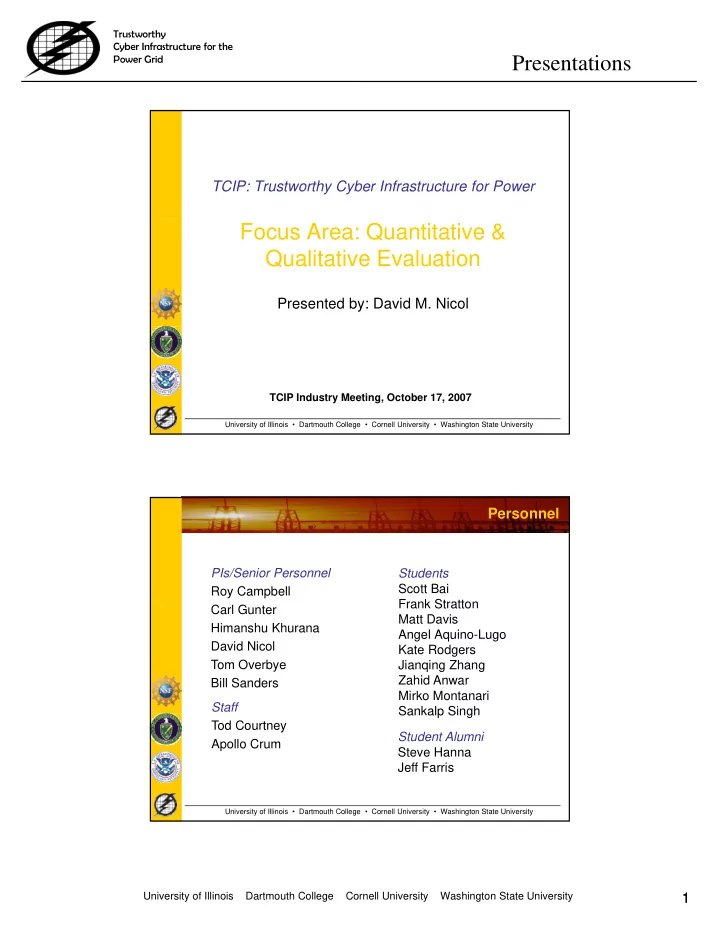
TCIP: Trustworthy Cyber Infrastructure for Power
Focus Area: Quantitative & Qualitative Evaluation
Presented by: David M. Nicol
University of Illinois • Dartmouth College • Cornell University • Washington State University
TCIP Industry Meeting, October 17, 2007
Personnel
PIs/Senior Personnel Roy Campbell C l G t Students Scott Bai Frank Stratton Carl Gunter Himanshu Khurana David Nicol Tom Overbye Bill Sanders Staff Frank Stratton Matt Davis Angel Aquino-Lugo Kate Rodgers Jianqing Zhang Zahid Anwar Mirko Montanari Sankalp Singh
University of Illinois • Dartmouth College • Cornell University • Washington State University