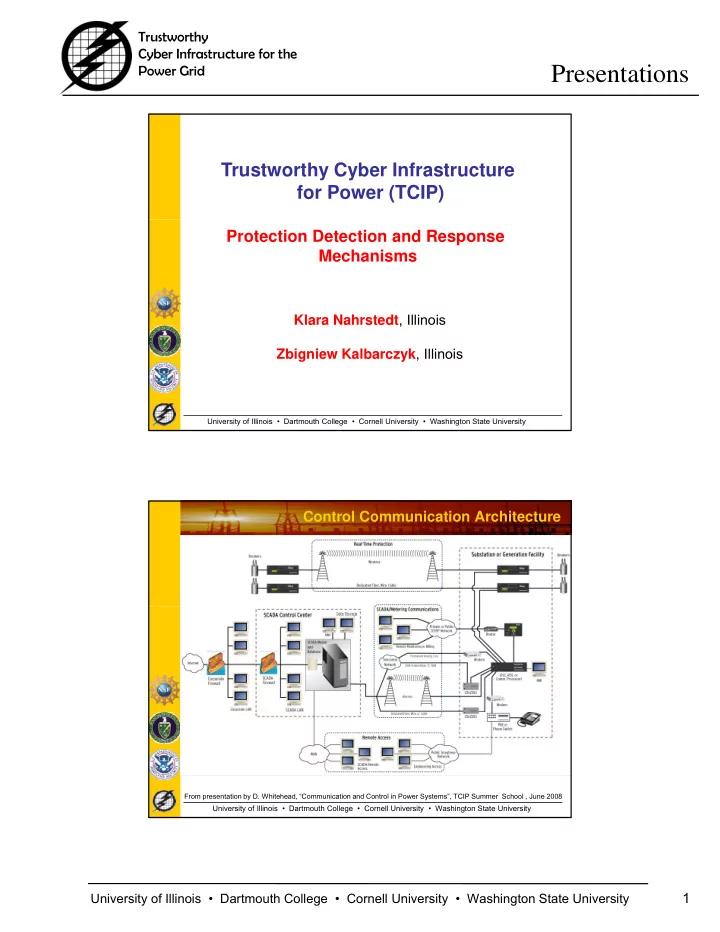
SLIDE 4 Trustworthy Cyber Infrastructure for the Power Grid
Presentations
University of Illinois • Dartmouth College • Cornell University • Washington State University
4 Approach: End-to-End Real-Time Trust Provisioning via Protection, Detection, Response
Control Center Level
ISO
Ethernet / IP-Network (Secure, Real-time, Monitored)
Backup
Ethernet / IP-Network (Secure, Real-time, Monitored)
Coordinator Level
Private IP-Based Network (Secure, Real-time, Monitored) Private IP-Based Network (Secure, Real-time, Monitored)
Data “Smart” Gateway/Hub
Private IP-Based Network (Secure, Real-time, Monitored)
Network Level Metering and Load Control
University of Illinois • Dartmouth College • Cornell University • Washington State University
Substation Level Sensor/Actuator Level
IED IED IED Local HMI IED DFR IED IED IED “Smart” Gateway/Hub Ethernet / IP-Network (Secure, Real-time, Monitored)
Approach
– Protect: Prevent (Plan, Admit, Reserve) violations, Enforce (Schedule, Encrypt, Sign) real- ti il bilit i t it d
Data
Protection Functions Detection Functions Response Functions
Control Center
time availability, integrity and confidentiality – Detect: Monitor, Assess and Alert violations, threats, vulnerabilities, misbehaviors, errors
Private IP-Based Network (Secure, Real-time, Monitored)
DFR IEDIEDIED
Protection Functions Detection Functions Response Functions University of Illinois • Dartmouth College • Cornell University • Washington State University
– Respond: Act against abnormal events , Issue reconfigurations, Bridge new and legacy entities along the end-to-end path, Contain misbehaved entities
IED IED IED Local HMI IED
Protection Functions Detection Functions Response Functions
Substation