SLIDE 10 University of Illinois • Dartmouth College • Cornell University • Washington State University
Trustworthy Cyber Infrastructure for the Power Grid
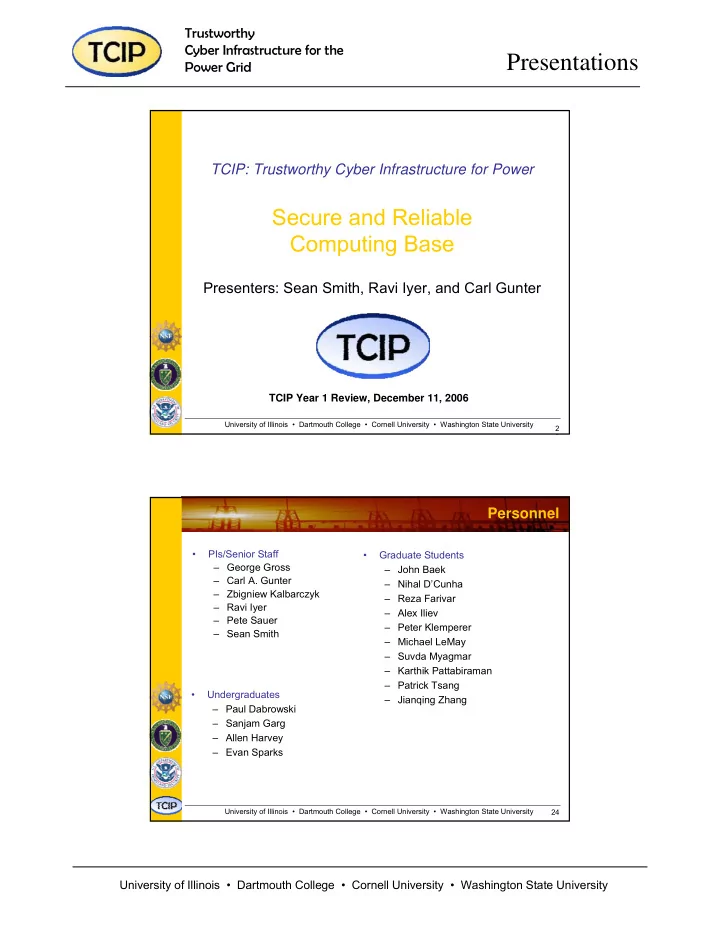
Presentations
41 University of Illinois • Dartmouth College • Cornell University • Washington State University OS Middleware Applications Hardware
Framework Interface Fabric P ip e lin e M o d u le s
Application Aware Trust: Support at Architectural Level
- Illinois Reliability and Security Engine (RSE)
– Reconfigurable processor-level hardware framework to support security and reliability
– Pointer Taintedness Module: protects against malicious tampering with data used by application
– Infinite Loop Hang Detection Module: protects against infinite program execution hangs
– FPGA-based trusted coprocessor which integrates: superscalar DLX core, RSE framework, and RSE hardware modules – Communication over PCI Bus with host computing system
42 University of Illinois • Dartmouth College • Cornell University • Washington State University
Fetch_Out
Instruction
RegFile_Data1 Source Operand 1 RegFile_Data2 Source Operand 2
Opcode Taint Bits Taint Bits M U X Ø jr? M U X Shift specific logic AND specific logic XOR specific logic Compare specific logic M U X Ø (ld/st)? alert alert Output Taint bits ALU Taintedness Tracking Logic Data Pointer Taintedness Detector Jump Pointer Taintedness Detector
Pipeline Outputs
RSE Framework
Fetch_Out RegFile_Data Execute_Out Memory_Out Commit_Out
Commit MEM EX ID IF
Instruction Queue Pre-emptive Control-flow Checking Process Health Monitor Selective Replication
Manager
Mem Mem_Rdy Reg#/ Reg Vals ALU Result Addr / Next PC Data Loaded From Memory Commit/ Squash
Pointer Taintedness Tracking
Framework Interface Fabric
Hardware Modules
INST
Reliability and Security Engine
Implementation: RSE with Pointer Taintedness Tracking and Detection Module