1
- 1
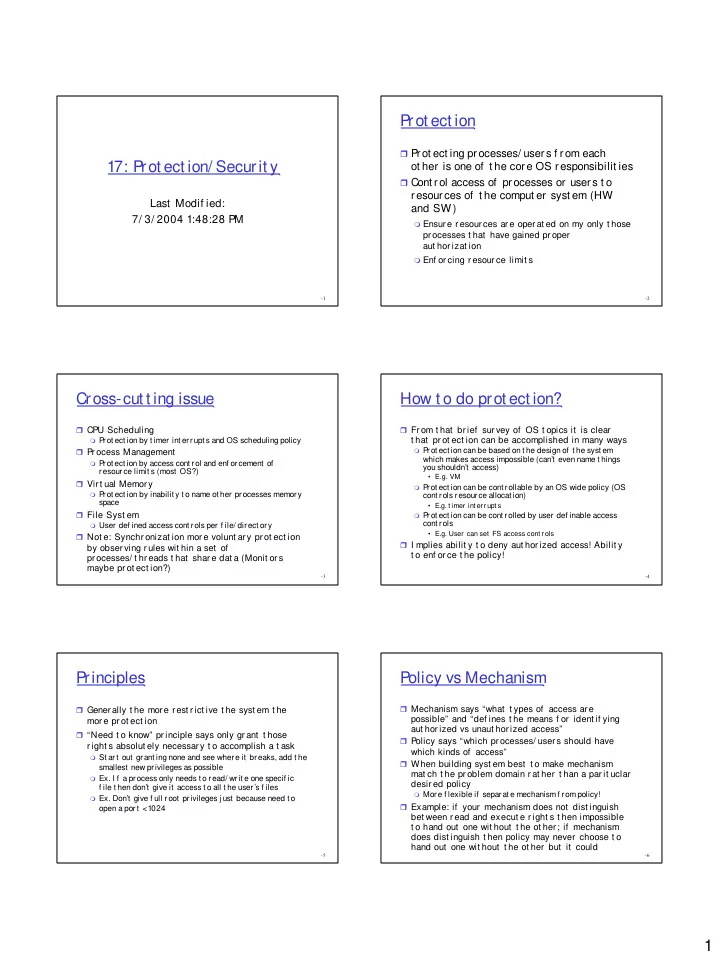
17: P rot ect ion/ Securit y
Last Modif ied: 7/ 3/ 2004 1:48:28 PM
- 2
P rot ect ion
Prot ect ing processes/ users f rom each
- t her is one of t he core OS responsibilit ies
Cont rol access of processes or users t o
resources of t he comput er syst em (HW and SW)
Ensur e r esour ces ar e oper at ed on my only t hose
pr ocesses t hat have gained pr oper aut hor izat ion
Enf or cing r esour ce limit s
- 3
Cross-cut t ing issue
CPU Scheduling
P
rot ect ion by t imer int errupt s and OS scheduling policy Pr ocess Management
P
rot ect ion by access cont rol and enf orcement of r esour ce limit s (most OS?) Vir t ual Memor y
P
rot ect ion by inabilit y t o name ot her processes memory space File Syst em
User def ined access cont rols per f ile/ direct ory
Not e: Synchr onizat ion mor e volunt ar y pr ot ect ion
by obser ving r ules wit hin a set of pr ocesses/ t hr eads t hat shar e dat a (Monit or s maybe pr ot ect ion?)
- 4
How t o do prot ect ion?
Fr om t hat br ief sur vey of OS t opics it is clear
t hat pr ot ect ion can be accomplished in many ways
P
rot ect ion can be based on t he design of t he syst em which makes access impossible (can’t even name t hings you shouldn’t access)
- E.g. VM
P
rot ect ion can be cont rollable by an OS wide policy (OS cont rols resource allocat ion)
- E.g. t imer int errupt s
P
rot ect ion can be cont rolled by user def inable access cont rols
- E.g. User can set FS access cont r ols
I mplies abilit y t o deny aut hor ized access! Abilit y
t o enf or ce t he policy!
- 5
P rinciples
Generally t he more rest rict ive t he syst em t he
mor e pr ot ect ion
“Need t o know” pr inciple says only gr ant t hose
r ight s absolut ely necessar y t o accomplish a t ask
St art out grant ing none and see where it breaks, add t he
smallest new privileges as possible
- Ex. I f a process only needs t o read/ writ e one specif ic
f ile t hen don’t give it access t o all t he user’s f iles
- Ex. Don’t give f ull root privileges j ust because need t o
- pen a por t <
1024
- 6
Policy vs Mechanism
Mechanism says “what t ypes of access ar e
possible” and “def ines t he means f or ident if ying aut hor ized vs unaut hor ized access”
Policy says “which pr ocesses/ user s should have
which kinds of access”
When building syst em best t o make mechanism
mat ch t he pr oblem domain r at her t han a par it uclar desir ed policy
More f lexible if separat e mechanism f rom policy!