1
Lecture 8 Page 1 CS 239, Winter 2005
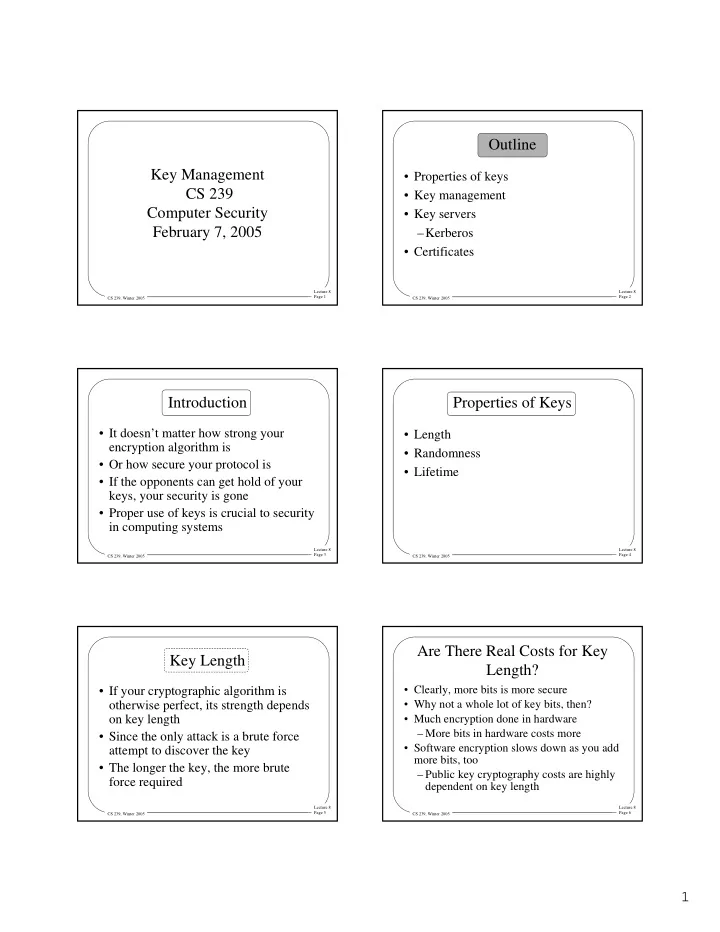
Key Management CS 239 Computer Security February 7, 2005
Lecture 8 Page 2 CS 239, Winter 2005
Outline
- Properties of keys
- Key management
- Key servers
–Kerberos
- Certificates
Lecture 8 Page 3 CS 239, Winter 2005
Introduction
- It doesn’t matter how strong your
encryption algorithm is
- Or how secure your protocol is
- If the opponents can get hold of your
keys, your security is gone
- Proper use of keys is crucial to security
in computing systems
Lecture 8 Page 4 CS 239, Winter 2005
Properties of Keys
- Length
- Randomness
- Lifetime
Lecture 8 Page 5 CS 239, Winter 2005
Key Length
- If your cryptographic algorithm is
- therwise perfect, its strength depends
- n key length
- Since the only attack is a brute force
attempt to discover the key
- The longer the key, the more brute
force required
Lecture 8 Page 6 CS 239, Winter 2005
Are There Real Costs for Key Length?
- Clearly, more bits is more secure
- Why not a whole lot of key bits, then?
- Much encryption done in hardware
– More bits in hardware costs more
- Software encryption slows down as you add